Come attractions, what we can look forward too.
Big Brother is watching you: The town where EVERY car is tracked by police cameras
A sleepy Home Counties market town has become the first in Britain to have every car passing through it tracked by police cameras.
Royston, in Hertfordshire, has had a set of police cameras installed on every road leading in and out of it, recording the numberplate of every vehicle that passes them.
The automatic number-plate recognition system will check the plates against a variety of databases, studying them for links to crimes, and insurance and tax records, and alerting police accordingly.
There were just seven incidents of vehicle crime in the town last month, and residents believe the unmarked cameras are an invasion of their privacy.
Quaint... and under surveillance: Royston, Hertfordshire is a small town with low-level crime, but is being monitored by the new police system
The system, due to be switched on in the next few days, also allows police to compile 'hotlists' of vehicles that they are interested in and which will be flagged up when the ANPR system
Details of the cars movements will stay on police records for two years, or five if the car is connected to a crime, the Guardian reported.
More...Sat-nav racers: Dangerous new craze sweeps Britain as drivers bid to 'beat the clock'
Mother who pocketed nearly £32k in disability hand-outs by claiming she was almost bed-ridden was caught shopping, driving and working as a nurse
The system, which is operated regionally, has sparked fears that the data could be abused and has led to claims that it is a big brother network that the public are completely oblivious of.
Guy Herbert, general secretary from NO2ID, which campaigns against databases storing the public's details, said: 'It's very sinister and quite creepy.
'They can approach anyone they like, but there's no legal basis for them doing so.
'There's no way to regulate how they use ANPR, they are the authority on it and they have their own rules.
'So there's no way to protect people's privacy.'
Mr Herbert also takes issue with the fact that the cameras are not advertised to the motorist, so many are unaware they have even been caught on the camera.
But Inspector Andy Piper, the ANPR manager for Hertfordshire and Bedfordshire, and a Royston resident himself, insists that the system will not be abused.
He told the Guardian: 'We only deal with people we're interested in stopping - that's the criminal element that comes into our county intent on committing crime, and unsafe drivers, disqualified drivers, or people driving uninsured vehicles, who we want to take off the road.'
Watching you: The ANPR cameras have been installed in the roads leading in and out of Royston
The ANPR cameras, which are not usually advertised to the public, seem bizarre given Royston's low level of crime. The town has a population of 15,000.
Following the most recent meeting of the Royston Neighbourhood Panel, it was decided that the local top priority of speeding should be replaced by shoplifting.
So some have questioned why Hertfordshire Police have taken such measures to track all of cars coming in and out of the town, which borders the Cambridgeshire and Essex counties.
Former Royston mayor Rod Kennedy believes the system is targeting the wrong area and details of vehicles should be deleted, unless they have committed a crime or are not registered.
'I just feel that we are on this slippery slope where everything we do will be monitored. I don't see why the honest citizen in a rural area such as this should have their movements tracked.'
Peaceful: Royston May Fayre, Priory Memorial Gardens, Royston, is a quiet town
But Inspector Piper told the Mail that many businesses were in favour of the system.
'On first sight, the ANPR coverage of such a low crime town as Royston may seem an unusual choice, but ANPR works both as a deterrent and a detection tool.
'The local district council and local business group funded the cameras to help protect their businesses and local residents from crime.
'And when we look at the bigger picture in terms of Hertfordshire, as well as nationally, the position of the cameras makes a lot of sense strategically to target those criminals travelling into the county on the main roads in that area.'
The ANPR system uses a mixture of mobile cameras inside police cars and fixed installations in some locations.
Police argue it helps trace missing people and identify witnesses to help with crimes but James Welch, Legal Director for Liberty, a human rights campaigning group said there needs to be tougher rules to stop it from being vulnerable to misuse.
'ANPR technology captures an identifying marker – a car’s number plate – so has the capability to track and record an individual’s movements far more intrusively than CCTV,' he said.
'While there may be crime detection gains the potential for abuse is great.
'We need an informed debate about the extent and potential of this technology and proper statutory regulation is already long overdue.'
http://www.dailymail.co.uk/news/article-2020167/Big-Brother-watching-Every-car-Royston-tracked-police.html#ixzz1TafYHuDq
House panel approves broadened ISP snooping bill
Internet providers would be forced to keep logs of their customers' activities for one year--in case police want to review them in the future--under legislation that a U.S. House of Representatives committee approved today.
The 19 to 10 vote represents a victory for conservative Republicans, who made data retention their first major technology initiative after last fall's elections, and the Justice Department officials who have quietly lobbied for the sweeping new requirements, a development first reported by CNET.
House Judiciary committee prepares to vote on sweeping data retention mandate.
(Credit: U.S. House of Representatives) A last-minute rewrite of the bill expands the information that commercial Internet providers are required to store to include customers' names, addresses, phone numbers, credit card numbers, bank account numbers, and temporarily-assigned IP addresses, some committee members suggested. By a 7-16 vote, the panel rejected an amendment that would have clarified that only IP addresses must be stored.
It represents "a data bank of every digital act by every American" that would "let us find out where every single American visited Web sites," said Rep. Zoe Lofgren of California, who led Democratic opposition to the bill.
Lofgren said the data retention requirements are easily avoided because they only apply to "commercial" providers. Criminals would simply go to libraries or Starbucks coffeehouses and use the Web anonymously, she said, while law-abiding Americans would have their activities recorded.
To make it politically difficult to oppose, proponents of the data retention requirements dubbed the bill the Protecting Children From Internet Pornographers Act of 2011, even though the mandatory logs would be accessible to police investigating any crime and perhaps attorneys litigating civil disputes in divorce, insurance fraud, and other cases as well.
"The bill is mislabeled," said Rep. John Conyers of Michigan, the senior Democrat on the panel. "This is not protecting children from Internet pornography. It's creating a database for everybody in this country for a lot of other purposes."
ISP snooping time line
In events that were first reported by CNET, Justice Department officials have been lobbying to require Internet providers to track of what Americans are doing online. Here's the time line:
June 2005: Justice Department officials quietly propose data retention rules.
December 2005: European Parliament votes for data retention of up to two years.
April 2006: Data retention proposals surface in Colorado and the U.S. Congress.
April 2006: Attorney General Gonzales says data retention "must be addressed."
April 2006: Rep. DeGette proposes data retention amendment.
May 2006: Rep. Sensenbrenner drafts data retention legislation--but backs away from it two days later.
May 2006: Gonzales and FBI Director Mueller meet with Internet and telecommunications companies.
February 2009: Two data retention bills target ISPs, hotels, coffee shops
February 2009: Copyright holders would benefit from data retention
January 2011: Justice Department calls for mandatory data retention
February 2011: White House undecided on data retention
May 2011: Wireless providers exempted from Rep. Smith's bill
July 2011: National Sheriffs' Association endorses data retention
Supporters of the measure characterized it as something that would aid law enforcement in investigating Internet crimes. Not enacting it "would keep our law enforcement officials in the dark ages," said its primary sponsor, House Judiciary chairman Lamar Smith (R-Texas).
"Both Democratic and Republican administrations have called for data retention for over a decade," said Smith, who noted that groups including the National Sheriffs' Association, the Major County Sheriffs' Association, and the Fraternal Order of Police have endorsed the concept.
For a while, it seemed like opposition from a handful of conservative members of Congress, coupled with Democrats concerned about civil liberties, would derail the bill.
Rep. F. James Sensenbrenner, a Wisconsin Republican and previous chairman of the House Judiciary committee, had criticized it at a hearing earlier this month, and again in the voting session that began yesterday and continued through this morning.
"I oppose this bill," said Sensenbrenner. "It can be amended, but I don't think it can be fixed... It poses numerous risks that well outweigh any benefits, and I'm not convinced it will contribute in a significant way to protecting children."
So did Rep. Jason Chaffetz (R-Utah), who has made privacy a signature issue and introduced a geolocation bill last month after trying to curb the use of airport body-scanners two years ago.
The original version of the bill, introduced in May, required Internet providers to "retain for a period of at least 18 months the temporarily assigned network addresses the service assigns to each account, unless that address is transmitted by radio communication." The wireless exemption appeared to be the result of lobbying from major carriers, but drew the ire of the Justice Department, which says it didn't go far enough, and was removed in a revised draft.
The mobile exemption represents a new twist in the debate over data retention requirements, which has been simmering since the Justice Department pushed the topic in 2005, a development that was first reported by CNET. Proposals publicly surfaced in the U.S. Congress the following year, and President Bush's attorney general, Alberto Gonzales said it's an issue that "must be addressed." So, eventually, did FBI director Robert Mueller.
In January 2011, CNET was the first to report that the Obama Justice Department was following suit. Jason Weinstein, the deputy assistant attorney general for the criminal division, warned that wireless providers must be included because "when this information is not stored, it may be impossible for law enforcement to collect essential evidence."
Smith introduced a broadly similar bill in 2007, without the wireless exemption, calling it a necessary anti-cybercrime measure. "The legislation introduced today will give law enforcement the tools it needs to find and prosecute criminals," he said in a statement at the time.
"Retention" vs. "preservation"
At the moment, Internet service providers typically discard any log file that's no longer required for business reasons such as network monitoring, fraud prevention, or billing disputes. Companies do, however, alter that general rule when contacted by police performing an investigation--a practice called data preservation.
A 1996 federal law called the Electronic Communication Transactional Records Act regulates data preservation. It requires Internet providers to retain any "record" in their possession for 90 days "upon the request of a governmental entity."
Because Internet addresses remain a relatively scarce commodity, ISPs tend to allocate them to customers from a pool based on whether a computer is in use at the time. (Two standard techniques used are the Dynamic Host Configuration Protocol and Point-to-Point Protocol over Ethernet.)
In addition, an existing law called the Protect Our Children Act of 2008 requires any Internet provider who "obtains actual knowledge" of possible child pornography transmissions to "make a report of such facts or circumstances." Companies that knowingly fail to comply can be fined up to $150,000 for the first offense and up to $300,000 for each subsequent offense.
http://news.cnet.com/8301-31921_3-20084939-281/house-panel-approves-broadened-isp-snooping-bill/
Your Silence shows your Consent. It is easy to hope for the best, when you are prepared for the worst.
Saturday, July 30, 2011
Friday, July 29, 2011
Friday 07-29-11
ATF position on pistol grip 'shotguns' creates new danger
An interpretation by the Bureau of Alcohol, Tobacco, Firearms and Explosives that pistol grip shotguns are not shotguns has created an unforeseen legal liability for owners of such firearms. ATF’s Nov. 2009 FFL Newsletter declared:
Certain commercially produced firearms do not fall within the definition of shotgun under the GCA even though they utilize a shotgun shell for ammunition. For example, firearms that come equipped with a pistol grip in place of the buttstock are not shotguns as defined by the GCA.
Here’s another wrinkle, from Mike Vanderboegh at Sipsey Street Irregulars:
An October 27, 2010, letter from the Firearms Technology Branch ruled that such a firearm, with a 17" barrel and 26-1/4" overall length, was not subject to the National Firearms Act.
You can click here to read the letter.
That would seem to indicate there’s no issue with violating National Firearms Registration and Transfer Record (NFRTR) requirements, right? No worries if you own one, or want to buy one…?
Not so fast. If the pistol grip firearms are not “shotguns,” what are they?
The NFA Owners Association points us to the only “legal” definition seemingly available with which to classify these firearms (click on link for “National Firearms Act (NFA) of 1934, as amended” to open up the text):
[T]aken at face value, a "pistol grip firearm" with a bore diameter larger than 1/2" in diameter is a "Destructive Device" under the NFA, unless the Attorney General determines that it is "a shotgun . . . generally recognized as particularly suitable for sporting purposes." By determining that a "pistol grip firearm" is not a shotgun, it is difficult to understand how current law would not classify such as firearm as a Destructive Device."
A “Destructive Device”?
"Any weapon by whatever name known which will, or which may be readily converted to, expel a projectile by the action of an explosive or other propellant, the barrel or barrels of which have a bore of more than one-half inch in diameter, except a shotgun or shotgun shell which the Secretary finds is generally recognized as particularly suitable for sporting purposes." Source: 26 U.S.C, Section 5845(f).
Which means registration on the NFRTR would be required. But there’s no way to do that retroactively, is there?
Per Vanderboegh:
http://www.examiner.com/gun-rights-in-national/atf-position-on-pistol-grip-shotguns-creates-new-danger
AWOL soldier condemned '09 Fort Hood shootings
KILLEEN, Texas (AP) - As Pfc. Naser Abdo beseeched officials to grant him conscientious objector status and release him from the military, he condemned a fellow Muslim soldier accused of shooting 13 people to death at Fort Hood. Such acts, he wrote, "run counter to what I believe in as a Muslim."
Less than a year later, officials say Abdo has admitted planning to launch another attack on Fort Hood with a bomb in a backpack and weapons stashed in a motel room where he was arrested Wednesday, about 3 miles from the Texas Army base's main gate.
The 21-year-old's writings, including the essay obtained by The Associated Press in which he deplored the 2009 shootings, portray a devout infantry soldier struggling with his faith while facing the prospect of deployment and what he felt was the scorn of his peers.
"Overall, as a Muslim I feel that I will not be able to carry out my military duties due to my conscientious objection," Abdo wrote in his application for the status. "Therefore, unless I separate myself from the military, I would potentially be putting the soldiers I work with in jeopardy.
"In this instance, I would be failing in my duty to my unit, my army and my god."
Abdo was approved as a conscientious objector this year, but his discharge was put on hold amid military charges that 34 images of child pornography were found on a computer he used. He went absent without leave from Fort Campbell, Ky., during the July 4 weekend.
On July 3, Abdo tried to buy a gun at a store near the Kentucky post, according to the company that owns the store. Abdo told an AP reporter a week later that he was concerned about his safety and had considered purchasing a gun for protection, but had not yet done so.
Police in Killeen said their break in the case came Tuesday from Guns Galore LLC _ the same gun store where Maj. Nidal Hasan bought a pistol used in the 2009 attack. Store clerk Greg Ebert said Abdo arrived by taxi and bought 6 pounds of smokeless gunpowder, three boxes of shotgun ammunition and a magazine for a semi-automatic pistol.
Ebert said he called authorities because he and his co-workers "felt uncomfortable with his overall demeanor and the fact he didn't know what the hell he was buying."
"We would probably be here today, giving you a different briefing, had he not been stopped," said Killeen Police Chief Dennis Baldwin, who called the plan "a terror plot."
According to an Army alert sent via email and obtained by the AP, Killeen police learned from the taxi company that Abdo had been picked up from a local motel and also had visited an Army surplus store where he paid cash for a uniform bearing Fort Hood unit patches.
Agents found firearms and "items that could be identified as bomb-making components, including gunpowder," in Abdo's motel room, FBI spokesman Erik Vasys said. The FBI planned to charge Abdo with possessing bomb-making materials.
An Oklahoma lawyer who has represented Abdo said Thursday he hadn't heard him in weeks. "I've been quite anxious to get in touch with him," said attorney James Branum.
The Army alert said Abdo "was in possession of a large quantity of ammunition, weapons and a bomb inside a backpack," and upon questioning admitted planning an attack on Fort Hood.
The military's criminal investigation division, along with the federal Joint Terrorism Task Force, had previously investigated Abdo after he was flagged for making unspecified anti-American comments while taking a language class, according to a U.S. official briefed on the investigation.
The official, who spoke on condition of anonymity because the investigation is ongoing, said neither the military nor the task force discovered anything at the time to indicate Abdo was planning an attack, the official said.
As the first anniversary of the 2009 Fort Hood rampage approached, Abdo sent to the AP the essay describing how he became a "different Muslim" after going through basic training at Fort Benning, Ga., and enduring religious harassment.
"Often times, during basic training the trainees would insult Islam and insult Muslims," he wrote. As a result, Abdo said he grew reclusive and stopped socializing.
Abdo grew up in Garland, a Dallas suburb about 170 miles from Fort Hood. In his essay, he said his mother is Christian and his father is Muslim, and that he decided to follow Islam when he was 17
"Little did I know that when I first became a Muslim that I was going to learn what Islam meant to me and what I was willing to sacrifice for it," he wrote.
Abdo said life was better after he arrived at his first duty station, but that he studied Islam more closely as he neared deployment to learn "whether going to war was the right thing to do Islamically."
"I began to understand and believe that only God can give legitimacy to war and not humankind," he wrote. "That's when I realized my conscience would not allow me to deploy."
His application was filed in June 2010. Abdo wrote that if it was granted, he looked forward to "rejoining the Muslim community in Dallas and spending some time on `The path of Allah." He said he would devote days or weeks travelling to other states and sleeping in mosques to "revive the faith of the Muslim nation."
The Army's Conscientious Objector Review board denied his request, but the deputy assistant secretary of the Army Review Boards Agency recommended this year he be separated from the Army as a conscientious objector. The discharge was delayed when he was charged with possession of child pornography on May 13.
Fort Campbell civilian spokesman Bob Jenkins said Abdo had been aware of the child pornography investigation since November.
Abdo attempted to purchase a gun July 3 from Quantico Tactical, a store near Fort Campbell in Oak Grove, Ky., said David Hensley, president of the seven-store chain.
Hensley said Abdo went into the store twice that day. The first time, after asking questions, he left. The second time, he attempted to buy a handgun, Hensley said.
"He exhibited behavior that alerted our staff and our staff refused to, based upon that behavior, sell him a firearm," he said.
The AP was among the media outlets to interview Abdo in the past year when reporting on his request for objector status. On July 12, Abdo contacted an AP reporter with whom he had spoken previously, said he had gone AWOL and considered purchasing a gun for personal protection. Abdo said he had not yet done so, because he knew he would have to give his name and other information to the gun dealer.
The AP described the contents of this conversation on July 14 to a civilian Army spokesman. The next day, when contacted by Army investigators, the AP said it did not know Abdo's location and provided the telephone number from which he made his original call.
http://wtop.com/?nid=209&sid=2474043
Ark. soldier shooter sent FBI letter
A man who pleaded guilty to shooting two soldiers outside a military recruiting station in Arkansas said he also shot at the home of a rabbi in Little Rock days earlier, according to a letter he wrote to the FBI.
In the letter obtained by The Associated Press under a Freedom of Information Act request, Abdulhakim Muhammad said he fired 10 rounds at the home of Rabbi Eugene Levy days before he fatally shot Pvt. William Andrew Long and wounded Pvt. Quinton Ezeagwula in June 2009.
A judge sentenced Muhammad to life in prison without parole this week after prosecutors accepted his plea agreement during his capital murder trial for killing Long and hurting Ezeagwula.
In the letter, dated November 24, 2009, Muhammad said he targeted Levy's house after researching Jewish leaders in Little Rock, Nashville, Tenn., and his hometown of Memphis, where he was born by the name Carlos Bledsoe. He changed his name after converting to Islam in college.
"Figured the FBI wasn't watching me anymore," he wrote. "I started my Plans to Attack, recruitment centers, Jewish organizations, across America..." He said he bought rifles, a pistol, ammunition and materials to make Molotov cocktails.
Then, shortly after midnight May 30, Muhammad said he shot at Levy's house from his truck using a .22-caliber rifle.
"The spent rounds were found during search," he wrote.
Levy's wife, Bobbye Levy, said FBI agents visited their home sometime in June after Muhammad was arrested. But she said she didn't hear any gunshots or find any damage to the house.
"We never knew anything about it until the FBI showed up," she said.
She wasn't sure whether the agents found any remnants of a shooting outside. FBI spokesman Steve Frazier declined to comment.
Levy said and her husband, who's a rabbi at Temple B'nai Israel in Little Rock, have never received any threatening letters or phone calls.
Muhammad said he then drove to Memphis and later Nashville to the homes of two other rabbis. In Nashville, he said he drove to a Jewish community center, "but found there were too many children around so I aborted that."
So, the self-professed jihadist said he kept driving until he came to a recruitment center in Florence, Ky., but found it was closed.
He decided to go back to Little Rock to revise his plan, and said he drove overnight to Nashville. About 2 a.m. on June 1, Muhammad said he decided to firebomb another rabbi's house. He said he lobbed a Molotov cocktail at the home, but the fire blew out mid-air.
"Another attempt gone sour," he wrote.
He made it to Little Rock that morning and spotted two uniformed soldiers outside a military recruiting center in Little Rock. He said he considered firing at them from afar, but decided to get closer so he wouldn't miss.
He fired an assault rifle at Long and Ezeagwula, who were smoking cigarettes outside. They had recently completed basic training and decided to volunteer as recruiters. Neither had seen combat.
Muhammad rolled down the window and fired an assault rifle. Ezeagwula, then 18, watched his friend fall to the ground as the bullets hit them. In the parking lot, Long's mother, Janet Long, heard the gunshots.
In his letter to the FBI, Muhammad confessed to his actions, taking full responsibility and professing ties to al-Qaida. He told The Associated Press that the shootings were justified because of U.S. military actions in the Middle East.
"I ask to be punish by lethal injection and to be shown no respite," he wrote to the FBI.
http://wtop.com/?nid=209&sid=2341907
An interpretation by the Bureau of Alcohol, Tobacco, Firearms and Explosives that pistol grip shotguns are not shotguns has created an unforeseen legal liability for owners of such firearms. ATF’s Nov. 2009 FFL Newsletter declared:
Certain commercially produced firearms do not fall within the definition of shotgun under the GCA even though they utilize a shotgun shell for ammunition. For example, firearms that come equipped with a pistol grip in place of the buttstock are not shotguns as defined by the GCA.
Here’s another wrinkle, from Mike Vanderboegh at Sipsey Street Irregulars:
An October 27, 2010, letter from the Firearms Technology Branch ruled that such a firearm, with a 17" barrel and 26-1/4" overall length, was not subject to the National Firearms Act.
You can click here to read the letter.
That would seem to indicate there’s no issue with violating National Firearms Registration and Transfer Record (NFRTR) requirements, right? No worries if you own one, or want to buy one…?
Not so fast. If the pistol grip firearms are not “shotguns,” what are they?
The NFA Owners Association points us to the only “legal” definition seemingly available with which to classify these firearms (click on link for “National Firearms Act (NFA) of 1934, as amended” to open up the text):
[T]aken at face value, a "pistol grip firearm" with a bore diameter larger than 1/2" in diameter is a "Destructive Device" under the NFA, unless the Attorney General determines that it is "a shotgun . . . generally recognized as particularly suitable for sporting purposes." By determining that a "pistol grip firearm" is not a shotgun, it is difficult to understand how current law would not classify such as firearm as a Destructive Device."
A “Destructive Device”?
"Any weapon by whatever name known which will, or which may be readily converted to, expel a projectile by the action of an explosive or other propellant, the barrel or barrels of which have a bore of more than one-half inch in diameter, except a shotgun or shotgun shell which the Secretary finds is generally recognized as particularly suitable for sporting purposes." Source: 26 U.S.C, Section 5845(f).
Which means registration on the NFRTR would be required. But there’s no way to do that retroactively, is there?
Per Vanderboegh:
http://www.examiner.com/gun-rights-in-national/atf-position-on-pistol-grip-shotguns-creates-new-danger
AWOL soldier condemned '09 Fort Hood shootings
KILLEEN, Texas (AP) - As Pfc. Naser Abdo beseeched officials to grant him conscientious objector status and release him from the military, he condemned a fellow Muslim soldier accused of shooting 13 people to death at Fort Hood. Such acts, he wrote, "run counter to what I believe in as a Muslim."
Less than a year later, officials say Abdo has admitted planning to launch another attack on Fort Hood with a bomb in a backpack and weapons stashed in a motel room where he was arrested Wednesday, about 3 miles from the Texas Army base's main gate.
The 21-year-old's writings, including the essay obtained by The Associated Press in which he deplored the 2009 shootings, portray a devout infantry soldier struggling with his faith while facing the prospect of deployment and what he felt was the scorn of his peers.
"Overall, as a Muslim I feel that I will not be able to carry out my military duties due to my conscientious objection," Abdo wrote in his application for the status. "Therefore, unless I separate myself from the military, I would potentially be putting the soldiers I work with in jeopardy.
"In this instance, I would be failing in my duty to my unit, my army and my god."
Abdo was approved as a conscientious objector this year, but his discharge was put on hold amid military charges that 34 images of child pornography were found on a computer he used. He went absent without leave from Fort Campbell, Ky., during the July 4 weekend.
On July 3, Abdo tried to buy a gun at a store near the Kentucky post, according to the company that owns the store. Abdo told an AP reporter a week later that he was concerned about his safety and had considered purchasing a gun for protection, but had not yet done so.
Police in Killeen said their break in the case came Tuesday from Guns Galore LLC _ the same gun store where Maj. Nidal Hasan bought a pistol used in the 2009 attack. Store clerk Greg Ebert said Abdo arrived by taxi and bought 6 pounds of smokeless gunpowder, three boxes of shotgun ammunition and a magazine for a semi-automatic pistol.
Ebert said he called authorities because he and his co-workers "felt uncomfortable with his overall demeanor and the fact he didn't know what the hell he was buying."
"We would probably be here today, giving you a different briefing, had he not been stopped," said Killeen Police Chief Dennis Baldwin, who called the plan "a terror plot."
According to an Army alert sent via email and obtained by the AP, Killeen police learned from the taxi company that Abdo had been picked up from a local motel and also had visited an Army surplus store where he paid cash for a uniform bearing Fort Hood unit patches.
Agents found firearms and "items that could be identified as bomb-making components, including gunpowder," in Abdo's motel room, FBI spokesman Erik Vasys said. The FBI planned to charge Abdo with possessing bomb-making materials.
An Oklahoma lawyer who has represented Abdo said Thursday he hadn't heard him in weeks. "I've been quite anxious to get in touch with him," said attorney James Branum.
The Army alert said Abdo "was in possession of a large quantity of ammunition, weapons and a bomb inside a backpack," and upon questioning admitted planning an attack on Fort Hood.
The military's criminal investigation division, along with the federal Joint Terrorism Task Force, had previously investigated Abdo after he was flagged for making unspecified anti-American comments while taking a language class, according to a U.S. official briefed on the investigation.
The official, who spoke on condition of anonymity because the investigation is ongoing, said neither the military nor the task force discovered anything at the time to indicate Abdo was planning an attack, the official said.
As the first anniversary of the 2009 Fort Hood rampage approached, Abdo sent to the AP the essay describing how he became a "different Muslim" after going through basic training at Fort Benning, Ga., and enduring religious harassment.
"Often times, during basic training the trainees would insult Islam and insult Muslims," he wrote. As a result, Abdo said he grew reclusive and stopped socializing.
Abdo grew up in Garland, a Dallas suburb about 170 miles from Fort Hood. In his essay, he said his mother is Christian and his father is Muslim, and that he decided to follow Islam when he was 17
"Little did I know that when I first became a Muslim that I was going to learn what Islam meant to me and what I was willing to sacrifice for it," he wrote.
Abdo said life was better after he arrived at his first duty station, but that he studied Islam more closely as he neared deployment to learn "whether going to war was the right thing to do Islamically."
"I began to understand and believe that only God can give legitimacy to war and not humankind," he wrote. "That's when I realized my conscience would not allow me to deploy."
His application was filed in June 2010. Abdo wrote that if it was granted, he looked forward to "rejoining the Muslim community in Dallas and spending some time on `The path of Allah." He said he would devote days or weeks travelling to other states and sleeping in mosques to "revive the faith of the Muslim nation."
The Army's Conscientious Objector Review board denied his request, but the deputy assistant secretary of the Army Review Boards Agency recommended this year he be separated from the Army as a conscientious objector. The discharge was delayed when he was charged with possession of child pornography on May 13.
Fort Campbell civilian spokesman Bob Jenkins said Abdo had been aware of the child pornography investigation since November.
Abdo attempted to purchase a gun July 3 from Quantico Tactical, a store near Fort Campbell in Oak Grove, Ky., said David Hensley, president of the seven-store chain.
Hensley said Abdo went into the store twice that day. The first time, after asking questions, he left. The second time, he attempted to buy a handgun, Hensley said.
"He exhibited behavior that alerted our staff and our staff refused to, based upon that behavior, sell him a firearm," he said.
The AP was among the media outlets to interview Abdo in the past year when reporting on his request for objector status. On July 12, Abdo contacted an AP reporter with whom he had spoken previously, said he had gone AWOL and considered purchasing a gun for personal protection. Abdo said he had not yet done so, because he knew he would have to give his name and other information to the gun dealer.
The AP described the contents of this conversation on July 14 to a civilian Army spokesman. The next day, when contacted by Army investigators, the AP said it did not know Abdo's location and provided the telephone number from which he made his original call.
http://wtop.com/?nid=209&sid=2474043
Ark. soldier shooter sent FBI letter
A man who pleaded guilty to shooting two soldiers outside a military recruiting station in Arkansas said he also shot at the home of a rabbi in Little Rock days earlier, according to a letter he wrote to the FBI.
In the letter obtained by The Associated Press under a Freedom of Information Act request, Abdulhakim Muhammad said he fired 10 rounds at the home of Rabbi Eugene Levy days before he fatally shot Pvt. William Andrew Long and wounded Pvt. Quinton Ezeagwula in June 2009.
A judge sentenced Muhammad to life in prison without parole this week after prosecutors accepted his plea agreement during his capital murder trial for killing Long and hurting Ezeagwula.
In the letter, dated November 24, 2009, Muhammad said he targeted Levy's house after researching Jewish leaders in Little Rock, Nashville, Tenn., and his hometown of Memphis, where he was born by the name Carlos Bledsoe. He changed his name after converting to Islam in college.
"Figured the FBI wasn't watching me anymore," he wrote. "I started my Plans to Attack, recruitment centers, Jewish organizations, across America..." He said he bought rifles, a pistol, ammunition and materials to make Molotov cocktails.
Then, shortly after midnight May 30, Muhammad said he shot at Levy's house from his truck using a .22-caliber rifle.
"The spent rounds were found during search," he wrote.
Levy's wife, Bobbye Levy, said FBI agents visited their home sometime in June after Muhammad was arrested. But she said she didn't hear any gunshots or find any damage to the house.
"We never knew anything about it until the FBI showed up," she said.
She wasn't sure whether the agents found any remnants of a shooting outside. FBI spokesman Steve Frazier declined to comment.
Levy said and her husband, who's a rabbi at Temple B'nai Israel in Little Rock, have never received any threatening letters or phone calls.
Muhammad said he then drove to Memphis and later Nashville to the homes of two other rabbis. In Nashville, he said he drove to a Jewish community center, "but found there were too many children around so I aborted that."
So, the self-professed jihadist said he kept driving until he came to a recruitment center in Florence, Ky., but found it was closed.
He decided to go back to Little Rock to revise his plan, and said he drove overnight to Nashville. About 2 a.m. on June 1, Muhammad said he decided to firebomb another rabbi's house. He said he lobbed a Molotov cocktail at the home, but the fire blew out mid-air.
"Another attempt gone sour," he wrote.
He made it to Little Rock that morning and spotted two uniformed soldiers outside a military recruiting center in Little Rock. He said he considered firing at them from afar, but decided to get closer so he wouldn't miss.
He fired an assault rifle at Long and Ezeagwula, who were smoking cigarettes outside. They had recently completed basic training and decided to volunteer as recruiters. Neither had seen combat.
Muhammad rolled down the window and fired an assault rifle. Ezeagwula, then 18, watched his friend fall to the ground as the bullets hit them. In the parking lot, Long's mother, Janet Long, heard the gunshots.
In his letter to the FBI, Muhammad confessed to his actions, taking full responsibility and professing ties to al-Qaida. He told The Associated Press that the shootings were justified because of U.S. military actions in the Middle East.
"I ask to be punish by lethal injection and to be shown no respite," he wrote to the FBI.
http://wtop.com/?nid=209&sid=2341907
Thursday, July 28, 2011
Thursday 07-28-11
Long-term, universal flu shot on horizon
A universal flu vaccine that protects against all strains may be within reach in the next five years, replacing annual shots developed for specifics flu viruses, the chief of the National Institutes of Health predicts.
By Jack Gruber, USA TODAY
Dr. Francis Collins, director of the National Institutes of Health, says a universal flu vaccine may be within reach in the next five years.
Francis Collins told USA TODAY's Editorial Board on Tuesday that he is "guardedly optimistic" about development of a long-term shot to replace the one "you'd have to renew every year."
About 200,000 people are hospitalized with the flu every year, and an estimated 3,000 to 49,000 die, making the flu one of the chief causes of preventable death in the USA.
Collins cited the long-term flu shot in a wide-ranging discussion of many advances coming from NIH research. Amid budget debates now underway in Washington, D.C. that could also trim NIH's $31billion budget, he made the case for research investments that improve the nation's health.
VIDEO: 5 questions with NIH Director Francis Collins
A universal flu vaccine "seemed completely out of reach only a few years ago," Collins said. That's because flu viruses mutate yearly, causing small changes in surface coatings, which make old vaccines obsolete.
Recently however, scientists have found "there are parts of the viral coat that don't change …. If you designed a vaccine to go after the constant part of the virus, you'd be protected against all strains," Collins said.
A universal flu vaccine is "not a question of whether, but when," says Arnold Monto, of the University of Michigan. "I think five years is a bit ambitious, given where we are now."
Scientists around the world are working on the problem. In February, researchers in the United Kingdom reported preliminary success developing a universal flu vaccine in humans.
Collins pointed to other advances springing from investment in biomedical research:
• Alzheimer's studies suggest inflammation, rather than brain-tangling proteins, triggers many cases of the dementia that afflicts more than 5million, according to NIH.
• Diabetes research is finding that exercise and nutrition coaching is more effective at checking symptoms than drug treatment.
•HIV studies suggest screening everyone in the country for HIV could lead to early treatment to prevent some of the 56,000 new cases each year.
"We might be able to end this epidemic," Collins said. Given that the lifetime cost of HIV/AIDS treatment is $1million — a total of $56billion to treat just the newly infected each year — universal screening "begins to look cost-effective." He cautioned there is no proposal for such screening.
NIH already runs pilot programs to test and treat high-risk people in Washington, D.C. and the Bronx, N.Y., says Anthony Fauci, head of NIH's National Institute of Allergy and Infectious Diseases. "Scientifically, we know it works."
http://yourlife.usatoday.com/health/medical/coldflu/story/2011/07/Long-term-universal-flu-shot-on-horizon/49671698/1
You can take a look at the charts at the link, it is worth looking at.
Are We Broke Yet?
Two simple graphs, updated daily, that show exactly how screwed the federal government's finances really are.
Here's one way to express how catastrophically screwed the U.S. government's finances are: If the entire U.S budget were cut to zero, effective immediately—the military, all entitlements, the electricity bill for the Capitol—there still wouldn't be enough money to cover the payments on old debt that come due every day. In fact, by Slate's calculations, the payments would have dried us up in under a month. So for decades the strategy has been to borrow new money to pay down old debt—plus a little extra to kick to the Treasury's coffers, since we habitually spend more than we take in. That continued to work this year until May 16, when we maxed out our congressional credit card. Since then, the Treasury has been living on savings and whatever revenue comes in. The first graph here very simply shows the balance in the Treasury's bank account, which is published every weekday. The light-colored bars at the end represent the Bipartisan Policy Center's projections for how long we can make it before the money all dries up. That date is Aug. 3.
Update, July 26, 10:12 a.m.: The most recent Treasury statement, for July 22, reports a balance of $84.4 billion, slightly below projections. Funds are still on track to run dry on Wednesday, Aug. 3.
Below it is a graph of the total national debt. Note that the scale begins at $13.5 trillion, not zero.
Jul
July 14, 2011
$14.294 trillion
As you can see, as the debt approaches the point of no return, the U.S. coffers take a major hit. But you will also see some spikes in revenue after borrowing is maxed out. This can be attributed to many things—an influx of tax revenue, profits from the Federal Reserve's holdings, and the general movement of funds and debt between accounts. We are continuing to borrow money as well, but only in equal amounts to the debt we pay off, so as to remain under the debt ceiling.
http://www.slate.com/id/2299845/
When al Qaeda is defeated, can we have our liberties back?
Last week brought the unsurprising news that the Transportation Security Administration had terrorized yet another 6-year-old with a humiliating pat-down. Dog bites man, federal agent gropes child -- we're getting all too accustomed to this sort of thing in post-9/11 America.
Meanwhile, even the administration's top terror warriors are starting to admit that al Qaeda is a spent force. Two weeks ago, in his first public comments after moving from Langley to the Pentagon, Defense Secretary Leon Panetta noted that al Qaeda's defeat was "within reach."
When we kill or round up some 10 to 20 remaining senior operatives, Panetta said, we'll "really cripple al Qaeda as a threat to this country." In fact, the al Qaeda threat has looked anything but robust for some time now.
Last summer, al Qaeda's online journal Inspire, a sort of Soldier of Fortune magazine for wannabe jihadis, suggested using "a tractor or farm vehicle in an attack outfitted with blades or swords as a fearsome killing machine" -- perfect for "mowing down the enemies of Allah."
Among the treasure trove of materials seized from the Abbottabad compound was a missive from Osama bin Laden himself, condemning that scheme as "indiscriminate slaughter" -- an odd objection, coming from a mass murderer.
Yet somehow, the terrorist mastermind missed the more obvious objection: The plan is utterly screwball -- an embarrassment -- the dumbest scheme since ... well, since al Qaeda operative Iyman Faris' 2002 plan to cut down the Brooklyn Bridge with a blowtorch. As I've said before, sometimes you get the sense that these guys aren't the sharpest scimitars in the shed.
The global intelligence firm Stratfor put it more politely in a recent analysis: "The jihadists seem to be having a problem ... finding people who can master the terrorist tradecraft" and travel freely to the West.
They've been reduced to urging potential sympathizers who already live here to stock up at gun shows and shoot some infidels at the mall. But, as Stratfor observes, "the very call to leaderless resistance is an admission of defeat."
We may be winning, but don't dare imagine that "victory" will take the form of a restoration of lost liberties. That's "defeatist" thinking. I suppose that's why, shortly after SEAL Team 6 killed bin Laden, Congress and the president's autopen got together to reauthorize the Patriot Act. The threat recedes, but the surveillance state must live on.
And there can be no talk of beating porno-scanners into plowshares. The Department of Homeland Security recently warned that terrorists might "surgically implant explosive devices" in their bodies.
Slate.com reports that several firms are already hard at work on scanners that can look inside our bodies instead of just inside our clothes. Like all other bureaucracies, the bureaucracy of fear has a merciless logic of its own. It exists to exist, generating new invasions of privacy -- and new federal contracts -- however speculative the threats.
Ten days after the Sept. 11 attacks, in a speech to a joint session of Congress, President George W. Bush laid out his vision of al Qaeda's demise: heirs to the "murderous ideologies of the 20th century," they'd end up "in history's unmarked grave of discarded lies."
Nearly a decade later, U.S. Navy SEALs pitched the head murderer's body off the side of the USS Carl Vinson into the North Arabian Sea -- a watery grave that's a pretty close approximation of Bush's imagery.
Wired magazine defense analyst Spencer Ackerman asks the right question: "Why does the U.S. still need to devote such overwhelming resources worldwide against a force that's seeing history pass it by?"
As the 10th anniversary of the Sept. 11 attacks approaches, isn't it time we started thinking about a "peace dividend"?
http://washingtonexaminer.com/opinion/columnists/2011/07/when-al-qaeda-defeated-can-we-have-our-liberties-back#ixzz1TK2fu7eO
A universal flu vaccine that protects against all strains may be within reach in the next five years, replacing annual shots developed for specifics flu viruses, the chief of the National Institutes of Health predicts.
By Jack Gruber, USA TODAY
Dr. Francis Collins, director of the National Institutes of Health, says a universal flu vaccine may be within reach in the next five years.
Francis Collins told USA TODAY's Editorial Board on Tuesday that he is "guardedly optimistic" about development of a long-term shot to replace the one "you'd have to renew every year."
About 200,000 people are hospitalized with the flu every year, and an estimated 3,000 to 49,000 die, making the flu one of the chief causes of preventable death in the USA.
Collins cited the long-term flu shot in a wide-ranging discussion of many advances coming from NIH research. Amid budget debates now underway in Washington, D.C. that could also trim NIH's $31billion budget, he made the case for research investments that improve the nation's health.
VIDEO: 5 questions with NIH Director Francis Collins
A universal flu vaccine "seemed completely out of reach only a few years ago," Collins said. That's because flu viruses mutate yearly, causing small changes in surface coatings, which make old vaccines obsolete.
Recently however, scientists have found "there are parts of the viral coat that don't change …. If you designed a vaccine to go after the constant part of the virus, you'd be protected against all strains," Collins said.
A universal flu vaccine is "not a question of whether, but when," says Arnold Monto, of the University of Michigan. "I think five years is a bit ambitious, given where we are now."
Scientists around the world are working on the problem. In February, researchers in the United Kingdom reported preliminary success developing a universal flu vaccine in humans.
Collins pointed to other advances springing from investment in biomedical research:
• Alzheimer's studies suggest inflammation, rather than brain-tangling proteins, triggers many cases of the dementia that afflicts more than 5million, according to NIH.
• Diabetes research is finding that exercise and nutrition coaching is more effective at checking symptoms than drug treatment.
•HIV studies suggest screening everyone in the country for HIV could lead to early treatment to prevent some of the 56,000 new cases each year.
"We might be able to end this epidemic," Collins said. Given that the lifetime cost of HIV/AIDS treatment is $1million — a total of $56billion to treat just the newly infected each year — universal screening "begins to look cost-effective." He cautioned there is no proposal for such screening.
NIH already runs pilot programs to test and treat high-risk people in Washington, D.C. and the Bronx, N.Y., says Anthony Fauci, head of NIH's National Institute of Allergy and Infectious Diseases. "Scientifically, we know it works."
http://yourlife.usatoday.com/health/medical/coldflu/story/2011/07/Long-term-universal-flu-shot-on-horizon/49671698/1
You can take a look at the charts at the link, it is worth looking at.
Are We Broke Yet?
Two simple graphs, updated daily, that show exactly how screwed the federal government's finances really are.
Here's one way to express how catastrophically screwed the U.S. government's finances are: If the entire U.S budget were cut to zero, effective immediately—the military, all entitlements, the electricity bill for the Capitol—there still wouldn't be enough money to cover the payments on old debt that come due every day. In fact, by Slate's calculations, the payments would have dried us up in under a month. So for decades the strategy has been to borrow new money to pay down old debt—plus a little extra to kick to the Treasury's coffers, since we habitually spend more than we take in. That continued to work this year until May 16, when we maxed out our congressional credit card. Since then, the Treasury has been living on savings and whatever revenue comes in. The first graph here very simply shows the balance in the Treasury's bank account, which is published every weekday. The light-colored bars at the end represent the Bipartisan Policy Center's projections for how long we can make it before the money all dries up. That date is Aug. 3.
Update, July 26, 10:12 a.m.: The most recent Treasury statement, for July 22, reports a balance of $84.4 billion, slightly below projections. Funds are still on track to run dry on Wednesday, Aug. 3.
Below it is a graph of the total national debt. Note that the scale begins at $13.5 trillion, not zero.
Jul
July 14, 2011
$14.294 trillion
As you can see, as the debt approaches the point of no return, the U.S. coffers take a major hit. But you will also see some spikes in revenue after borrowing is maxed out. This can be attributed to many things—an influx of tax revenue, profits from the Federal Reserve's holdings, and the general movement of funds and debt between accounts. We are continuing to borrow money as well, but only in equal amounts to the debt we pay off, so as to remain under the debt ceiling.
http://www.slate.com/id/2299845/
When al Qaeda is defeated, can we have our liberties back?
Last week brought the unsurprising news that the Transportation Security Administration had terrorized yet another 6-year-old with a humiliating pat-down. Dog bites man, federal agent gropes child -- we're getting all too accustomed to this sort of thing in post-9/11 America.
Meanwhile, even the administration's top terror warriors are starting to admit that al Qaeda is a spent force. Two weeks ago, in his first public comments after moving from Langley to the Pentagon, Defense Secretary Leon Panetta noted that al Qaeda's defeat was "within reach."
When we kill or round up some 10 to 20 remaining senior operatives, Panetta said, we'll "really cripple al Qaeda as a threat to this country." In fact, the al Qaeda threat has looked anything but robust for some time now.
Last summer, al Qaeda's online journal Inspire, a sort of Soldier of Fortune magazine for wannabe jihadis, suggested using "a tractor or farm vehicle in an attack outfitted with blades or swords as a fearsome killing machine" -- perfect for "mowing down the enemies of Allah."
Among the treasure trove of materials seized from the Abbottabad compound was a missive from Osama bin Laden himself, condemning that scheme as "indiscriminate slaughter" -- an odd objection, coming from a mass murderer.
Yet somehow, the terrorist mastermind missed the more obvious objection: The plan is utterly screwball -- an embarrassment -- the dumbest scheme since ... well, since al Qaeda operative Iyman Faris' 2002 plan to cut down the Brooklyn Bridge with a blowtorch. As I've said before, sometimes you get the sense that these guys aren't the sharpest scimitars in the shed.
The global intelligence firm Stratfor put it more politely in a recent analysis: "The jihadists seem to be having a problem ... finding people who can master the terrorist tradecraft" and travel freely to the West.
They've been reduced to urging potential sympathizers who already live here to stock up at gun shows and shoot some infidels at the mall. But, as Stratfor observes, "the very call to leaderless resistance is an admission of defeat."
We may be winning, but don't dare imagine that "victory" will take the form of a restoration of lost liberties. That's "defeatist" thinking. I suppose that's why, shortly after SEAL Team 6 killed bin Laden, Congress and the president's autopen got together to reauthorize the Patriot Act. The threat recedes, but the surveillance state must live on.
And there can be no talk of beating porno-scanners into plowshares. The Department of Homeland Security recently warned that terrorists might "surgically implant explosive devices" in their bodies.
Slate.com reports that several firms are already hard at work on scanners that can look inside our bodies instead of just inside our clothes. Like all other bureaucracies, the bureaucracy of fear has a merciless logic of its own. It exists to exist, generating new invasions of privacy -- and new federal contracts -- however speculative the threats.
Ten days after the Sept. 11 attacks, in a speech to a joint session of Congress, President George W. Bush laid out his vision of al Qaeda's demise: heirs to the "murderous ideologies of the 20th century," they'd end up "in history's unmarked grave of discarded lies."
Nearly a decade later, U.S. Navy SEALs pitched the head murderer's body off the side of the USS Carl Vinson into the North Arabian Sea -- a watery grave that's a pretty close approximation of Bush's imagery.
Wired magazine defense analyst Spencer Ackerman asks the right question: "Why does the U.S. still need to devote such overwhelming resources worldwide against a force that's seeing history pass it by?"
As the 10th anniversary of the Sept. 11 attacks approaches, isn't it time we started thinking about a "peace dividend"?
http://washingtonexaminer.com/opinion/columnists/2011/07/when-al-qaeda-defeated-can-we-have-our-liberties-back#ixzz1TK2fu7eO
Wednesday, July 27, 2011
Wednesday 07-27-11

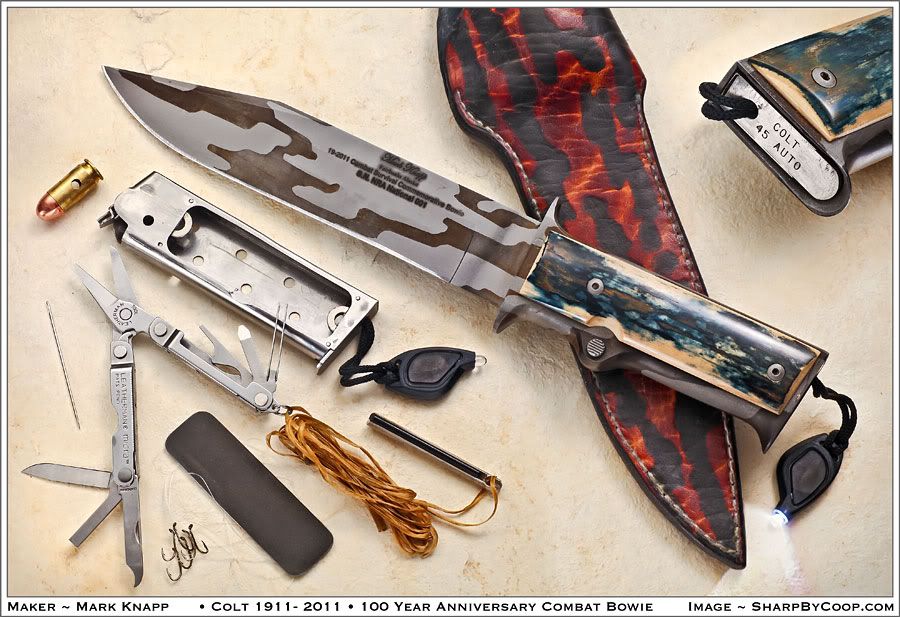
http://www.markknappcustomknives.com/
Street View cars grabbed locations of phones, PCs
scoop Google's Street View cars collected the locations of millions of laptops, cell phones, and other Wi-Fi devices around the world, a practice that raises novel privacy concerns, CNET has confirmed.
The cars were supposed to collect the locations of Wi-Fi access points. But Google also recorded the street addresses and unique identifiers of computers and other devices using those wireless networks and then made the data publicly available through Google.com until a few weeks ago.
The French data protection authority, known as the Commission Nationale de l'Informatique et des Libertés (CNIL) recently contacted CNET and said its investigation confirmed that Street View cars collected these unique hardware IDs. In March, CNIL's probe resulted in a fine of 100,000 euros, about $143,000.
The confirmation comes as concerns about location privacy appear to be growing. Apple came under fire in April for recording logs of approximate location data on iPhones, and eventually released a fix. That controversy sparked a series of disclosures about other companies' location privacy practices, questions and complaints from congressmen, a pair of U.S. Senate hearings, and the now-inevitable lawsuits seeking class action status.
A previous CNET article, published June 15 and triggered by the research of security consultant Ashkan Soltani, was the first to report that Google made these unique hardware IDs--called MAC addresses--publicly available through a Web interface. Google curbed the practice about a week later.
But it was unclear at the time whether Google's location database included the hardware IDs of only access points and wireless routers or client devices, such as computers and mobile phones, as well.
Anecdotal evidence suggested they had been swept up. Alissa Cooper, chief computer scientist at the Center for Democracy and Technology and co-chair of an Internet Engineering Task Force on geolocation, said her 2009 home address was listed in Google's location database. Nick Doty, a lecturer at the University of California at Berkeley who co-teaches the Technology and Policy Lab, found that Google listed his former home in the Capitol Hill neighborhood in Seattle.
"It would be helpful to have some clarity about why and how (a hardware address) got in there so people can act accordingly," says Soltani, the security researcher.
Security researcher Ashkan Soltani says a big problem is no opt-out method.
(Credit: Declan McCullagh/CNET) Google declined repeated requests for comment for this article over a period of more than a week. In a statement last month, the search company said only that "we collect the publicly broadcast MAC addresses of Wi-Fi access points," which addressed only current and not past practices.
Google does not provide any method, sometimes called an opt-out mechanism, that would allow people who don't want their unique hardware IDs in the database to remove them. Instead of using Street View cars, Google new "crowdsources" its location database by using Android phones.
The most likely explanation of how the Wi-Fi devices were included is the simplest: Just as an accident of programming led to Street View cars collecting (in relatively few cases) the contents of unencrypted wireless communications, client hardware addresses were also vacuumed up. Then they were added to Google's geolocation database, which was publicly available without access restrictions until late June.
Wi-Fi-enabled devices, including PCs, iPhones, iPads, and Android phones, transmit a unique hardware identifier to anyone within a radius of approximately 100 to 200 feet. If someone captured or already knew that unique address because they had access to the device, Google's application programming interface, or API, revealed where that device was located, a practice that can reveal personal information including home or work addresses or even the addresses of restaurants frequented.
To be sure, it's not always easy to learn a target's MAC address. It's generally not transmitted over the Internet. But anyone within Wi-Fi range can record it, and it's easy to narrow down which MAC addresses correspond to which manufacturer. Someone, such as a suspicious spouse, who can navigate to the About screen on an iPhone can obtain it that way too.
Kim Cameron, Microsoft's chief identity architect until earlier this year, had long suspected that Street View cars vacuumed up the hardware addresses of devices using a Wi-Fi connection. In a June 2010 essay that analyzed an independent report (PDF) of Street View data collection, Cameron said he believed that Google recorded the locations and MAC addresses of far more than just fixed Wi-Fi access points.
Marc Rotenberg, head of the Electronic Privacy Information Center in Washington, D.C., said he has concerns about the legality of intercepting the hardware addresses of devices using Wi-Fi connections.
"The fact that other companies such as Skyhook may have engaged in this behavior, which seems to be Google's best defense, doesn't make it lawful," Rotenberg said. "What it does suggest is that there's more to the investigation of Street View."
In the U.S., the Federal Trade Commission ended its investigation of Street View's accidentally-broad data collection last October without levying a fine.
http://news.cnet.com/8301-31921_3-20082777-281/street-view-cars-grabbed-locations-of-phones-pcs/
Tuesday, July 26, 2011
Tuesday 07-26-11
Bill to allow DHS to seize authority over U.S. coastlines
The House is currently considering a bill that would cede control of America’s coastlines to DHS.
Under the proposed National Security and Federal Lands Protection Act, the Secretary of the Interior would forfeit authority of all public coast lands to the Secretary of Homeland Security, whenever the DHS chief sees fit. The bill would also allow DHS to take control of lands located along the Canadian and Mexican borders. DHS would be empowered to freely construct roads and fences, deploy patrol vehicles, and set up “monitoring equipment” on these lands. Within 100 miles of a coastline or international border, DHS would also have the power to waive all environmental regulations including the Clean Air Act, the Safe Drinking Water Act, and the Coastal Zone Management Act.
The bill was introduced in April by Representative Rob Bishop (R – Utah) and has been referred to the House Committees on Natural Resources, Agriculture and Homeland Security.
According to the bill, its goal is to “prohibit the Secretaries of the Interior and Agriculture from taking action on public lands which impede border security on such lands, and for other purposes.”
Several lawmakers and environmental groups are already opposing the bill.
Lynn Scarlett, a former deputy Interior secretary under President George W. Bush, and Representative William Keating (D – Massachusetts), who sits on the House Homeland Security Committee, have strongly criticized the bill and requested further clarification.
“While HR 1505 is just starting to be reviewed by the appropriate committees and as such, is subject to extensive modification, Congressman Keating believes the legislation in its current form needs to be clarified so as to appropriately assess the border security risk levels of various locations throughout the country and balance our national security against other vital protections, such as environmental safeguards, which should not be discarded haphazardly,” said Lauren Amendolaro, the communications director for Representative Keating.
In addition, the Pew Environment Group argued that the bill is “sweeping waiver of the nation’s bedrock environmental and land management laws” and does little to help secure America’s borders.
Jane Danowitz, the director of U.S. public lands for the Pew Environment Group, said, “The proposed legislation would give unprecedented authority to a single federal agency to destroy wildlife habitat and wetlands, impair downstream water quality and restrict activities such as hunting, fishing and grazing. It would leave Congress and the public without a voice, even though at stake are hundreds of popular destinations.”
The bill would allow DHS to waive environmental laws across large swaths of areas like the entire Alaskan border, all of Hawaii, and all of Florida. In addition DHS could gain control of national parks like the Carlsbad Caverns in New Mexico, Acadia National Park in Maine, and Mount Rainer National Park in Washington.
http://www.homelandsecuritynewswire.com/bill-allow-dhs-seize-authority-over-us-coastlines
Web restrictions draw ire of some educators
Book banning has long been a controversial issue in the nation's schools. Now some educators say banned websites pose as great a threat to kids' education and intellectual freedom.
Most recently:
•New York City's Department of Education blocked Google Images last month for what it called "objectionable content" but later left it up to schools whether to allow it.
STORY: Social media finds place in classroom
•The Pinellas County (Fla.) School Board in June voted unanimously to block teachers from communicating with students via Facebook or Twitter, even about school-related matters. The school board said it hopes to prevent the appearance of inappropriate contact between students and teachers via social media.
This fall, a handful of schools and libraries across the USA plan to celebrate Banned Sites Day to draw attention to the issue, according to New Canaan (Conn.) High School librarian Michelle Luhtala. The day was her idea. She says the same issues of censorship, fear and free speech that make banned books resonate also apply to social-networking sites that most public schools block.
"Teaching with social media shows students how to responsibly use those platforms," Luhtala says. "Blocking access in schools denies kids the chance to practice sharing their knowledge with the real world in a supervised setting."
Many schools use "brute force" tools that block good educational sites, says Karen Cator, the U.S. Department of Education's director of educational technology. Cator says she has urged schools to use more sophisticated, updated software and to educate themselves on the actual filtering rules, which are less restrictive than many educators believe.
"The Internet is not going away," she says.
Along with social networking, many schools block teachers' personal e-mail and seemingly harmless sites. In a survey for the education website MindShift, Editor Tina Barseghian found that teachers at some schools couldn't access National Geographic or Flickr, as well as the video- conferencing site Skype.
http://www.usatoday.com/news/education/2011-07-25-banned-websites-school_n.htm
If you want a good look at the debt we owe, go to this site for an illistration.
http://www.wtfnoway.com/
The House is currently considering a bill that would cede control of America’s coastlines to DHS.
Under the proposed National Security and Federal Lands Protection Act, the Secretary of the Interior would forfeit authority of all public coast lands to the Secretary of Homeland Security, whenever the DHS chief sees fit. The bill would also allow DHS to take control of lands located along the Canadian and Mexican borders. DHS would be empowered to freely construct roads and fences, deploy patrol vehicles, and set up “monitoring equipment” on these lands. Within 100 miles of a coastline or international border, DHS would also have the power to waive all environmental regulations including the Clean Air Act, the Safe Drinking Water Act, and the Coastal Zone Management Act.
The bill was introduced in April by Representative Rob Bishop (R – Utah) and has been referred to the House Committees on Natural Resources, Agriculture and Homeland Security.
According to the bill, its goal is to “prohibit the Secretaries of the Interior and Agriculture from taking action on public lands which impede border security on such lands, and for other purposes.”
Several lawmakers and environmental groups are already opposing the bill.
Lynn Scarlett, a former deputy Interior secretary under President George W. Bush, and Representative William Keating (D – Massachusetts), who sits on the House Homeland Security Committee, have strongly criticized the bill and requested further clarification.
“While HR 1505 is just starting to be reviewed by the appropriate committees and as such, is subject to extensive modification, Congressman Keating believes the legislation in its current form needs to be clarified so as to appropriately assess the border security risk levels of various locations throughout the country and balance our national security against other vital protections, such as environmental safeguards, which should not be discarded haphazardly,” said Lauren Amendolaro, the communications director for Representative Keating.
In addition, the Pew Environment Group argued that the bill is “sweeping waiver of the nation’s bedrock environmental and land management laws” and does little to help secure America’s borders.
Jane Danowitz, the director of U.S. public lands for the Pew Environment Group, said, “The proposed legislation would give unprecedented authority to a single federal agency to destroy wildlife habitat and wetlands, impair downstream water quality and restrict activities such as hunting, fishing and grazing. It would leave Congress and the public without a voice, even though at stake are hundreds of popular destinations.”
The bill would allow DHS to waive environmental laws across large swaths of areas like the entire Alaskan border, all of Hawaii, and all of Florida. In addition DHS could gain control of national parks like the Carlsbad Caverns in New Mexico, Acadia National Park in Maine, and Mount Rainer National Park in Washington.
http://www.homelandsecuritynewswire.com/bill-allow-dhs-seize-authority-over-us-coastlines
Web restrictions draw ire of some educators
Book banning has long been a controversial issue in the nation's schools. Now some educators say banned websites pose as great a threat to kids' education and intellectual freedom.
Most recently:
•New York City's Department of Education blocked Google Images last month for what it called "objectionable content" but later left it up to schools whether to allow it.
STORY: Social media finds place in classroom
•The Pinellas County (Fla.) School Board in June voted unanimously to block teachers from communicating with students via Facebook or Twitter, even about school-related matters. The school board said it hopes to prevent the appearance of inappropriate contact between students and teachers via social media.
This fall, a handful of schools and libraries across the USA plan to celebrate Banned Sites Day to draw attention to the issue, according to New Canaan (Conn.) High School librarian Michelle Luhtala. The day was her idea. She says the same issues of censorship, fear and free speech that make banned books resonate also apply to social-networking sites that most public schools block.
"Teaching with social media shows students how to responsibly use those platforms," Luhtala says. "Blocking access in schools denies kids the chance to practice sharing their knowledge with the real world in a supervised setting."
Many schools use "brute force" tools that block good educational sites, says Karen Cator, the U.S. Department of Education's director of educational technology. Cator says she has urged schools to use more sophisticated, updated software and to educate themselves on the actual filtering rules, which are less restrictive than many educators believe.
"The Internet is not going away," she says.
Along with social networking, many schools block teachers' personal e-mail and seemingly harmless sites. In a survey for the education website MindShift, Editor Tina Barseghian found that teachers at some schools couldn't access National Geographic or Flickr, as well as the video- conferencing site Skype.
http://www.usatoday.com/news/education/2011-07-25-banned-websites-school_n.htm
If you want a good look at the debt we owe, go to this site for an illistration.
http://www.wtfnoway.com/
Monday, July 25, 2011
Saturday, July 23, 2011
Saturday 07-23-11
Bad idea in the first place, there is no need for another commission, they just don't need to do it.
UK scientists want human-animal tests monitored
British scientists say a new expert body should be formed to regulate experiments mixing animal and human DNA to make sure no medical or ethical boundaries are crossed.
In a report issued on Friday, scientists at the nation's Academy of Medical Sciences said a government organization is needed to advise whether certain tests on animals that use human DNA should be pursued.
Tighter regulation isn't needed for most such experiments, said Martin Bobrow, chair of the group that wrote the report. "But there are a small number of future experiments, which could approach social and ethically sensitive areas which should have an extra layer of scrutiny," he told reporters in London.
The group analyzed evidence from academics, the U.K. government, animal welfare groups and others. An independent survey was also conducted to gather public opinion. It found people were mostly supportive as long as the work might contribute to the development of medical treatments that would be widely available.
Scientists have long been swapping animal and human DNA. Numerous tests on mice with human genes for brain, bone and heart disorders are already under way and experiments on goats implanted with a human gene are also being done to study blood-clotting problems.
Controversy erupted several years ago in Britain after scientists announced plans to make human embryos with the nucleus removed from cow and rabbit eggs. Authorities allowed limited experiments and ruled the embryos should not be allowed to develop for more than two weeks.
In the latest report, Bobrow and colleagues concluded some experiments should only be allowed under additional monitoring from the new expert body and that a very small number of experiments should not be done at all.
Among experimentation that might spark concern are those where human brain cells might change animal brains, those that could lead to the fertilization of human eggs in animals and any modifications of animals that might create attributes considered uniquely human, like facial features, skin or speech.
Some disagree. "We think some of these should be done, but they should be done in an open way to maintain public confidence," said Robin Lovell-Badge, head of stem cell biology and developmental genetics at Britain's Medical Research Council, one of the expert group members. He said experiments injecting human brain cells into the brains of rats might help develop new stroke treatments or that growing human skin on mice could further understanding of skin cancer.
Other experts said such issues needed to be debated in Parliament and that any advisory body must have a diverse membership. "The danger is you could get scientists effectively regulating scientists," said Dr. Peter Saunders, chief executive of the Christian Medical Fellowship, a group that opposes the creation of human and animal embryos. He said most experiments on animals with human DNA were OK, but that any tests that aim to enhance animals with human material are not acceptable.
Bobrow warned altering animal brains with human brain cells shouldn't be done just yet. "The closer (an animal brain) is to a human brain, the harder it is to predict what might happen," he said.
Some members of the public surveyed about such potential experiments agreed. "I don't have a problem with it until it gets to the brain," said one respondent to an independent survey done for the Academy of Medical Sciences. "Bits to do with memories, that would be too far — it's a human thing to have a memory."
___
Online:
Academy of Medical Sciences: http://www.acmedsci.ac.uk
http://health.yahoo.net/news/s/ap/eu_med_animal_human_experiments
Parent complains after children were searched at pool
LANCASTER, Ohio -- About 65 children attending summer camp at the Robert K. Fox Family Y were told Tuesday to lower their bathing suits so counselors could visually inspect the suits after feces was found in the swimming pool.
That upset parent Ibrahim Y. Haroon, who said his 9-year-old son came home traumatized. He filed a complaint with the Lancaster police.
Now the Y is investigating what happened and reviewing its policies, Executive Director Mike Lieber said today.
Feces also was found in the pool on Monday and two other times within the last couple of weeks, he said. That could sicken the campers and the counselors in the water with them, he said.
The campers are in the fourth to sixth grades.
After the fourth occurrence on Tuesday, counselors asked the children if anyone was sick or had a problem. No one came forward. So, the child-care director who supervises the counselors directed them to take the children two by two into the girls and boys locker rooms and shower areas, require them to turn around facing away from the counselors, and lower their swim shorts for inspection, Lieber said.
The children then pulled up their bathing suits and showered, he said.
Haroon didn't like what he heard when his son came home.
"My child was very upset and seemed a bit traumatized," he said today. "His exact statement was it was very uncomfortable."
Haroon filed a police report and also talked to Lieber.
"I'm not sure that there was a criminal violation, but there was definitely a violation of his civil rights," he said. "Why weren't the parents notified before? If a search was going to be done, a child, like an adult, would have a right to due process."
Lieber said he reported the matter to Job and Family Services, which licenses the Y to run its school-age-child summer camp program, and was told that it would have been better to put the children, one by one, behind a privacy shield and have them hand out their suits to be inspected.
The inspections provided no clues to which child had diarrhea, Lieber said.
The pool was thoroughly cleaned and reopened yesterday, he said.
http://www.dispatch.com/live/content/local_news/stories/2011/07/21/pool-kids.html?sid=101
UK scientists want human-animal tests monitored
British scientists say a new expert body should be formed to regulate experiments mixing animal and human DNA to make sure no medical or ethical boundaries are crossed.
In a report issued on Friday, scientists at the nation's Academy of Medical Sciences said a government organization is needed to advise whether certain tests on animals that use human DNA should be pursued.
Tighter regulation isn't needed for most such experiments, said Martin Bobrow, chair of the group that wrote the report. "But there are a small number of future experiments, which could approach social and ethically sensitive areas which should have an extra layer of scrutiny," he told reporters in London.
The group analyzed evidence from academics, the U.K. government, animal welfare groups and others. An independent survey was also conducted to gather public opinion. It found people were mostly supportive as long as the work might contribute to the development of medical treatments that would be widely available.
Scientists have long been swapping animal and human DNA. Numerous tests on mice with human genes for brain, bone and heart disorders are already under way and experiments on goats implanted with a human gene are also being done to study blood-clotting problems.
Controversy erupted several years ago in Britain after scientists announced plans to make human embryos with the nucleus removed from cow and rabbit eggs. Authorities allowed limited experiments and ruled the embryos should not be allowed to develop for more than two weeks.
In the latest report, Bobrow and colleagues concluded some experiments should only be allowed under additional monitoring from the new expert body and that a very small number of experiments should not be done at all.
Among experimentation that might spark concern are those where human brain cells might change animal brains, those that could lead to the fertilization of human eggs in animals and any modifications of animals that might create attributes considered uniquely human, like facial features, skin or speech.
Some disagree. "We think some of these should be done, but they should be done in an open way to maintain public confidence," said Robin Lovell-Badge, head of stem cell biology and developmental genetics at Britain's Medical Research Council, one of the expert group members. He said experiments injecting human brain cells into the brains of rats might help develop new stroke treatments or that growing human skin on mice could further understanding of skin cancer.
Other experts said such issues needed to be debated in Parliament and that any advisory body must have a diverse membership. "The danger is you could get scientists effectively regulating scientists," said Dr. Peter Saunders, chief executive of the Christian Medical Fellowship, a group that opposes the creation of human and animal embryos. He said most experiments on animals with human DNA were OK, but that any tests that aim to enhance animals with human material are not acceptable.
Bobrow warned altering animal brains with human brain cells shouldn't be done just yet. "The closer (an animal brain) is to a human brain, the harder it is to predict what might happen," he said.
Some members of the public surveyed about such potential experiments agreed. "I don't have a problem with it until it gets to the brain," said one respondent to an independent survey done for the Academy of Medical Sciences. "Bits to do with memories, that would be too far — it's a human thing to have a memory."
___
Online:
Academy of Medical Sciences: http://www.acmedsci.ac.uk
http://health.yahoo.net/news/s/ap/eu_med_animal_human_experiments
Parent complains after children were searched at pool
LANCASTER, Ohio -- About 65 children attending summer camp at the Robert K. Fox Family Y were told Tuesday to lower their bathing suits so counselors could visually inspect the suits after feces was found in the swimming pool.
That upset parent Ibrahim Y. Haroon, who said his 9-year-old son came home traumatized. He filed a complaint with the Lancaster police.
Now the Y is investigating what happened and reviewing its policies, Executive Director Mike Lieber said today.
Feces also was found in the pool on Monday and two other times within the last couple of weeks, he said. That could sicken the campers and the counselors in the water with them, he said.
The campers are in the fourth to sixth grades.
After the fourth occurrence on Tuesday, counselors asked the children if anyone was sick or had a problem. No one came forward. So, the child-care director who supervises the counselors directed them to take the children two by two into the girls and boys locker rooms and shower areas, require them to turn around facing away from the counselors, and lower their swim shorts for inspection, Lieber said.
The children then pulled up their bathing suits and showered, he said.
Haroon didn't like what he heard when his son came home.
"My child was very upset and seemed a bit traumatized," he said today. "His exact statement was it was very uncomfortable."
Haroon filed a police report and also talked to Lieber.
"I'm not sure that there was a criminal violation, but there was definitely a violation of his civil rights," he said. "Why weren't the parents notified before? If a search was going to be done, a child, like an adult, would have a right to due process."
Lieber said he reported the matter to Job and Family Services, which licenses the Y to run its school-age-child summer camp program, and was told that it would have been better to put the children, one by one, behind a privacy shield and have them hand out their suits to be inspected.
The inspections provided no clues to which child had diarrhea, Lieber said.
The pool was thoroughly cleaned and reopened yesterday, he said.
http://www.dispatch.com/live/content/local_news/stories/2011/07/21/pool-kids.html?sid=101
Friday, July 22, 2011
Friday 07-22-11
Lawyer: Cop scanner ‘crosses line’
Civil libertarians are raising the alarm over the state’s plans to create a Big Brother database that could map drivers’ whereabouts with police cruiser-mounted scanners that capture thousands of license plates per hour — storing that information indefinitely where local cops, staties, feds and prosecutors could access it as they choose.
“What kind of a society are we creating here?” asked civil rights lawyer Harvey Silverglate, who along with the ACLU fears police abuse. “There comes a point where the surveillance is so pervasive and total that it’s a misnomer to call a society free any longer.”
The computerized scanners, known as Automatic License Plate Recognition devices, instantly check for police alerts, warrants, traffic violations and parking tickets, which cops say could be an invaluable tool in thwarting crime. The Executive Office of Public Safety has approved 27 grants totaling $500,000 to buy scanners for state police and 26 local departments. The purchases are on hold while state lawyers develop a policy for the use of a common state database all the scanners would feed.
Some ALPR scanners already are deployed on Massachusetts roads. State police have two. Several cities use them for parking enforcement. Chelsea has four scanner-mounted cruisers.
“It’s great for canvassing an area, say after a homicide if you are looking for a particular plate,” said Chelsea police Capt. Keith Houghton. “You can plug it in, and drive up and down side streets. It sounds an alarm if you get a hit.”
He said Chelsea’s information is overwritten after 30 days and is not shared with the state.
EOPS spokesman Terrell Harris said the state wants the scanner information fed into the Public Safety Data Center, where local, state and federal authorities could access it.
“We’re currently working to develop a policy that balances the effective use of this powerful law enforcement tool with the privacy concerns we’re keenly aware of,” Harris said.
The ACLU’s Kade Crockford said the technology, which just allows a faster version of what police do now in running plates, is less of a concern than the state’s plans to store information on average, law-abiding citizens.
“People who aren’t wanted for a crime, all of their information is stored in a database that is shared with another government agency,” Crawford said. “The potential for abuse is very big. We don’t think people who haven’t committed a crime should be tracked by law enforcement.”
The two state police cruisers equipped with scanners patrol the metro Boston area, state police spokesman David Procopio said. He defended police use of the new technology.
“What about the rights of someone who is already a victim to have their assailant brought to justice?” Procopio asked. “There’s a freedom to being able to live your life not worried about being the victim of crime that’s also a freedom worth protecting.”
Silverglate countered, “If you have cameras everywhere, of course you’re going to reduce the crime rate, but you’re not going to have a society worth preserving. To the American people, freedom means something. There is a line to draw in the sand, beyond which you don’t want the government poking its nose. This crosses the line.”
http://www.bostonherald.com/news/regional/view.bg?articleid=1353264
TSA says it's making airport screening more 'private'
The Transportation Security Administration said Wednesday that it has begun installing software to give passengers more privacy when they're screened by some of the full-body scanning machines at airport checkpoints.
The TSA says the software for millimeter-wave body-scanning machines, which use electromagnetic waves to screen passengers, replaces a passenger's image with a generic one that will still expose any dangerous items that could be hidden.
It also says that the software's automatic detection capability eliminates the need for a TSA agent to look at a passenger's image in a viewing room.
Many fliers have objected to having their "naked" images viewed by TSA personnel.
"This software upgrade enables us to continue providing a high level of security through advanced imaging technology screening, while improving the passenger experience at checkpoints," TSA Administrator John Pistole said Wednesday.
The TSA says it expects all 241 millimeter-wave machines at 40 U.S. airports to be upgraded by the end of the year.
The agency plans to test similar software in the fall for its 247 body-scanning "backscatter" devices, which use high-speed X-rays and emit a low dose of radiation. The backscatter machines are at 38 airports.
The move doesn't appease some consumer and privacy advocates who say the machines are a waste of money and represent an unlawful, virtual strip search of passengers. They also are concerned that radiation from the X-ray devices could be harmful.
"The machines are not effective, so the new software is throwing money at a solution that's not a solution," says Kate Hanni, executive director of FlyersRights.org. "The machines won't find low-density powdered explosives, liquid explosives — or much more than the old metal detectors."
TSA spokesman Nicholas Kimball says the machines "are the best technology currently available to detect well-concealed non-metallic explosives, which are among the most significant threats to our national security today."
Ginger McCall of the Electronic Privacy Information Center — a group that focuses attention on civil liberties issues — says it's unclear whether the new software will eliminate privacy concerns. She says the TSA must be more transparent about the capabilities of the software.
"If the software is simply an overlay which still permits the machines to capture, store or transfer the graphic naked image, then it doesn't solve the privacy problems created by these machines," says McCall, a lawyer for the group.
http://travel.usatoday.com/flights/story/2011/07/TSA-says-its-making-airport-screening-more-private/49540660/1
Civil libertarians are raising the alarm over the state’s plans to create a Big Brother database that could map drivers’ whereabouts with police cruiser-mounted scanners that capture thousands of license plates per hour — storing that information indefinitely where local cops, staties, feds and prosecutors could access it as they choose.
“What kind of a society are we creating here?” asked civil rights lawyer Harvey Silverglate, who along with the ACLU fears police abuse. “There comes a point where the surveillance is so pervasive and total that it’s a misnomer to call a society free any longer.”
The computerized scanners, known as Automatic License Plate Recognition devices, instantly check for police alerts, warrants, traffic violations and parking tickets, which cops say could be an invaluable tool in thwarting crime. The Executive Office of Public Safety has approved 27 grants totaling $500,000 to buy scanners for state police and 26 local departments. The purchases are on hold while state lawyers develop a policy for the use of a common state database all the scanners would feed.
Some ALPR scanners already are deployed on Massachusetts roads. State police have two. Several cities use them for parking enforcement. Chelsea has four scanner-mounted cruisers.
“It’s great for canvassing an area, say after a homicide if you are looking for a particular plate,” said Chelsea police Capt. Keith Houghton. “You can plug it in, and drive up and down side streets. It sounds an alarm if you get a hit.”
He said Chelsea’s information is overwritten after 30 days and is not shared with the state.
EOPS spokesman Terrell Harris said the state wants the scanner information fed into the Public Safety Data Center, where local, state and federal authorities could access it.
“We’re currently working to develop a policy that balances the effective use of this powerful law enforcement tool with the privacy concerns we’re keenly aware of,” Harris said.
The ACLU’s Kade Crockford said the technology, which just allows a faster version of what police do now in running plates, is less of a concern than the state’s plans to store information on average, law-abiding citizens.
“People who aren’t wanted for a crime, all of their information is stored in a database that is shared with another government agency,” Crawford said. “The potential for abuse is very big. We don’t think people who haven’t committed a crime should be tracked by law enforcement.”
The two state police cruisers equipped with scanners patrol the metro Boston area, state police spokesman David Procopio said. He defended police use of the new technology.
“What about the rights of someone who is already a victim to have their assailant brought to justice?” Procopio asked. “There’s a freedom to being able to live your life not worried about being the victim of crime that’s also a freedom worth protecting.”
Silverglate countered, “If you have cameras everywhere, of course you’re going to reduce the crime rate, but you’re not going to have a society worth preserving. To the American people, freedom means something. There is a line to draw in the sand, beyond which you don’t want the government poking its nose. This crosses the line.”
http://www.bostonherald.com/news/regional/view.bg?articleid=1353264
TSA says it's making airport screening more 'private'
The Transportation Security Administration said Wednesday that it has begun installing software to give passengers more privacy when they're screened by some of the full-body scanning machines at airport checkpoints.
The TSA says the software for millimeter-wave body-scanning machines, which use electromagnetic waves to screen passengers, replaces a passenger's image with a generic one that will still expose any dangerous items that could be hidden.
It also says that the software's automatic detection capability eliminates the need for a TSA agent to look at a passenger's image in a viewing room.
Many fliers have objected to having their "naked" images viewed by TSA personnel.
"This software upgrade enables us to continue providing a high level of security through advanced imaging technology screening, while improving the passenger experience at checkpoints," TSA Administrator John Pistole said Wednesday.
The TSA says it expects all 241 millimeter-wave machines at 40 U.S. airports to be upgraded by the end of the year.
The agency plans to test similar software in the fall for its 247 body-scanning "backscatter" devices, which use high-speed X-rays and emit a low dose of radiation. The backscatter machines are at 38 airports.
The move doesn't appease some consumer and privacy advocates who say the machines are a waste of money and represent an unlawful, virtual strip search of passengers. They also are concerned that radiation from the X-ray devices could be harmful.
"The machines are not effective, so the new software is throwing money at a solution that's not a solution," says Kate Hanni, executive director of FlyersRights.org. "The machines won't find low-density powdered explosives, liquid explosives — or much more than the old metal detectors."
TSA spokesman Nicholas Kimball says the machines "are the best technology currently available to detect well-concealed non-metallic explosives, which are among the most significant threats to our national security today."
Ginger McCall of the Electronic Privacy Information Center — a group that focuses attention on civil liberties issues — says it's unclear whether the new software will eliminate privacy concerns. She says the TSA must be more transparent about the capabilities of the software.
"If the software is simply an overlay which still permits the machines to capture, store or transfer the graphic naked image, then it doesn't solve the privacy problems created by these machines," says McCall, a lawyer for the group.
http://travel.usatoday.com/flights/story/2011/07/TSA-says-its-making-airport-screening-more-private/49540660/1
Thursday, July 21, 2011
Thursday 07-21-11
I guess they were guilty until they could prove they were innocent? Obiously others sold later in 2002, where did those come from?
Heirs Lose Fight With Gov't to Keep Rare Gold Coins
A jury has decided that a set of rare gold coins found in a bank deposit box rightfully belongs to the U.S. government.
The decision, made on Wednesday, caps an unusual civil case that combined history, coin collecting and whether the set of rare $20 "double eagles" should have ever let the U.S. Mint in 1933.
Federal prosecutors had asserted that the coins never circulated when the country went off the gold standard. Most of the batch was instead melted down.
But Joan Langbord, the daughter of a Philadelphia jeweler, said she found the 10 coins in her father's bank deposit bank after he died.
She said that her father could have acquired them legally, perhaps through a trade of gold scrap.
One 1933 double eagle sold for $7.6 million in 2002.
http://www.nbcphiladelphia.com/news/local/Heirs-Lose-Fight-With-Government-to-Keep-Dads-Rare-1933-Gold-Coins-125908579.html
Police to begin iPhone iris scans amid privacy concerns
Dozens of police departments nationwide are gearing up to use a tech company's already controversial iris- and facial-scanning device that slides over an iPhone and helps identify a person or track criminal suspects.
The so-called "biometric" technology, which seems to take a page from TV shows like "MI-5" or "CSI," could improve speed and accuracy in some routine police work in the field. However, its use has set off alarms with some who are concerned about possible civil liberties and privacy issues.
The smartphone-based scanner, named Mobile Offender Recognition and Information System, or MORIS, is made by BI2 Technologies in Plymouth, Massachusetts, and can be deployed by officers out on the beat or back at the station.
An iris scan, which detects unique patterns in a person's eyes, can reduce to seconds the time it takes to identify a suspect in custody. This technique also is significantly more accurate than results from other fingerprinting technology long in use by police, BI2 says.
When attached to an iPhone, MORIS can photograph a person's face and run the image through software that hunts for a match in a BI2-managed database of U.S. criminal records. Each unit costs about $3,000.
Some experts fret police may be randomly scanning the population, using potentially intrusive techniques to search for criminals, sex offenders, and illegal aliens, but the manufacturer says that would be a difficult task for officers to carry out.
Sean Mullin, BI2's CEO, says it is difficult, if not impossible, to covertly photograph someone and obtain a clear, usable image without that person knowing about it, because the MORIS should be used close up.
"It requires a level of cooperation that makes it very overt -- a person knows that you're taking a picture for this purpose," Mullin said.
CONCERNS
But constitutional rights advocates are concerned, in part because the device can accurately scan an individual's face from up to four feet away, potentially without a person's being aware of it.
Experts also say that before police administer an iris scan, they should have probable cause a crime has been committed.
"What we don't want is for them to become a general surveillance tool, where the police start using them routinely on the general public, collecting biometric information on innocent people," said Jay Stanley, senior policy analyst with the national ACLU in Washington, D.C.
Meanwhile, advocates see the MORIS as a way to make tools already in use on police cruiser terminals more mobile for cops on the job.
"This is (the technology) stepping out of the cruiser and riding on the officer's belt, along with his flashlight, his handcuffs, his sidearm or the other myriad tools," said John Birtwell, spokesman for the Plymouth County Sheriff's Department in southeastern Massachusetts, one of the first departments to use the devices.
The technology is also employed to maintain security at Plymouth's 1,650 inmate jail, where it is used to prevent the wrong prisoner from being released.
"There, we have everybody in orange jumpsuits, so everyone looks the same. So, quite literally, the last thing we do before you leave our facility is we compare your iris to our database," said Birtwell.
One of the technology's earliest uses at BI2, starting in 2005, was to help various agencies identify missing children or at-risk adults, like Alzheimer's patients.
Since then, it has been used to combat identity fraud, and could potentially be used in traffic stops when a driver is without a license, or when people are stopped for questioning at U.S. borders.
Facial recognition technology is not without its problems, however. For example, some U.S. individuals mistakenly have had their driver's license revoked as a potential fraud. The problem, it turns out, is that they look like another driver and so the technology mistakenly flags them as having fake identification.
Roughly 40 law enforcement units nationwide will soon be using the MORIS, including Arizona's Pinal County Sheriff's Office, as well as officers in Hampton City in Virginia and Calhoun County in Alabama.
http://www.reuters.com/article/2011/07/20/us-crime-identification-iris-idUSTRE76J4A120110720
Heirs Lose Fight With Gov't to Keep Rare Gold Coins
A jury has decided that a set of rare gold coins found in a bank deposit box rightfully belongs to the U.S. government.
The decision, made on Wednesday, caps an unusual civil case that combined history, coin collecting and whether the set of rare $20 "double eagles" should have ever let the U.S. Mint in 1933.
Federal prosecutors had asserted that the coins never circulated when the country went off the gold standard. Most of the batch was instead melted down.
But Joan Langbord, the daughter of a Philadelphia jeweler, said she found the 10 coins in her father's bank deposit bank after he died.
She said that her father could have acquired them legally, perhaps through a trade of gold scrap.
One 1933 double eagle sold for $7.6 million in 2002.
http://www.nbcphiladelphia.com/news/local/Heirs-Lose-Fight-With-Government-to-Keep-Dads-Rare-1933-Gold-Coins-125908579.html
Police to begin iPhone iris scans amid privacy concerns
Dozens of police departments nationwide are gearing up to use a tech company's already controversial iris- and facial-scanning device that slides over an iPhone and helps identify a person or track criminal suspects.
The so-called "biometric" technology, which seems to take a page from TV shows like "MI-5" or "CSI," could improve speed and accuracy in some routine police work in the field. However, its use has set off alarms with some who are concerned about possible civil liberties and privacy issues.
The smartphone-based scanner, named Mobile Offender Recognition and Information System, or MORIS, is made by BI2 Technologies in Plymouth, Massachusetts, and can be deployed by officers out on the beat or back at the station.
An iris scan, which detects unique patterns in a person's eyes, can reduce to seconds the time it takes to identify a suspect in custody. This technique also is significantly more accurate than results from other fingerprinting technology long in use by police, BI2 says.
When attached to an iPhone, MORIS can photograph a person's face and run the image through software that hunts for a match in a BI2-managed database of U.S. criminal records. Each unit costs about $3,000.
Some experts fret police may be randomly scanning the population, using potentially intrusive techniques to search for criminals, sex offenders, and illegal aliens, but the manufacturer says that would be a difficult task for officers to carry out.
Sean Mullin, BI2's CEO, says it is difficult, if not impossible, to covertly photograph someone and obtain a clear, usable image without that person knowing about it, because the MORIS should be used close up.
"It requires a level of cooperation that makes it very overt -- a person knows that you're taking a picture for this purpose," Mullin said.
CONCERNS
But constitutional rights advocates are concerned, in part because the device can accurately scan an individual's face from up to four feet away, potentially without a person's being aware of it.
Experts also say that before police administer an iris scan, they should have probable cause a crime has been committed.
"What we don't want is for them to become a general surveillance tool, where the police start using them routinely on the general public, collecting biometric information on innocent people," said Jay Stanley, senior policy analyst with the national ACLU in Washington, D.C.
Meanwhile, advocates see the MORIS as a way to make tools already in use on police cruiser terminals more mobile for cops on the job.
"This is (the technology) stepping out of the cruiser and riding on the officer's belt, along with his flashlight, his handcuffs, his sidearm or the other myriad tools," said John Birtwell, spokesman for the Plymouth County Sheriff's Department in southeastern Massachusetts, one of the first departments to use the devices.
The technology is also employed to maintain security at Plymouth's 1,650 inmate jail, where it is used to prevent the wrong prisoner from being released.
"There, we have everybody in orange jumpsuits, so everyone looks the same. So, quite literally, the last thing we do before you leave our facility is we compare your iris to our database," said Birtwell.
One of the technology's earliest uses at BI2, starting in 2005, was to help various agencies identify missing children or at-risk adults, like Alzheimer's patients.
Since then, it has been used to combat identity fraud, and could potentially be used in traffic stops when a driver is without a license, or when people are stopped for questioning at U.S. borders.
Facial recognition technology is not without its problems, however. For example, some U.S. individuals mistakenly have had their driver's license revoked as a potential fraud. The problem, it turns out, is that they look like another driver and so the technology mistakenly flags them as having fake identification.
Roughly 40 law enforcement units nationwide will soon be using the MORIS, including Arizona's Pinal County Sheriff's Office, as well as officers in Hampton City in Virginia and Calhoun County in Alabama.
http://www.reuters.com/article/2011/07/20/us-crime-identification-iris-idUSTRE76J4A120110720
Wednesday, July 20, 2011
Wednesday 07-20-11
Report: NRSC, Obama donor arrested as Pakistan agent
NBC reports:
Law enforcement sources say the FBI has arrested an agent of Pakistan's official state intelligence service, accusing him of making thousands of dollars in political contributions in the United States without disclosing his connections to the Pakistani government.
Syed Ghulam Fai will appear in federal court this afternoon in Alexandria, Va. He's not charged with being a spy. But he is charged with being an unregistered agent or lobbyist of the Pakistani government.
He's the exective director of a group called the Kashmiri American Council. ...
Fai's largest contribution, according to the Center for Responsive Politics, was to the National Republican Senatorial Committee, to which he gave $5,000 in 2006 and $1,000 in 2008. He gave smaller sums more recently to the DSCC and the DNC, and has given $5,000 to Rep. Dan Burton (R-Ind.), $250 to Barack Obama and $500 Rep. Yvette Clarke (D-N.Y.).
UPDATE: Brian Walsh, NRSC Communications Director, emails: “This pre-dates the current leadership at the NRSC but nonetheless it’s very disturbing and we’re happy to cooperate with any of the appropriate authorities investigating this matter.”
http://www.politico.com/blogs/bensmith/0711/Report_NRSC_Obama_donor_arrested_as_Pakistan_agent.html?showall
NBC reports:
Law enforcement sources say the FBI has arrested an agent of Pakistan's official state intelligence service, accusing him of making thousands of dollars in political contributions in the United States without disclosing his connections to the Pakistani government.
Syed Ghulam Fai will appear in federal court this afternoon in Alexandria, Va. He's not charged with being a spy. But he is charged with being an unregistered agent or lobbyist of the Pakistani government.
He's the exective director of a group called the Kashmiri American Council. ...
Fai's largest contribution, according to the Center for Responsive Politics, was to the National Republican Senatorial Committee, to which he gave $5,000 in 2006 and $1,000 in 2008. He gave smaller sums more recently to the DSCC and the DNC, and has given $5,000 to Rep. Dan Burton (R-Ind.), $250 to Barack Obama and $500 Rep. Yvette Clarke (D-N.Y.).
UPDATE: Brian Walsh, NRSC Communications Director, emails: “This pre-dates the current leadership at the NRSC but nonetheless it’s very disturbing and we’re happy to cooperate with any of the appropriate authorities investigating this matter.”
http://www.politico.com/blogs/bensmith/0711/Report_NRSC_Obama_donor_arrested_as_Pakistan_agent.html?showall
Monday, July 18, 2011
Monday 07-18-11
Just can't make up the stupidity
After Jail Time for Contempt, Alleged Rape Victim Returns to Testify
It's already extremely hard for rape victims to come to court and testify. This alleged rape victim says the only reason she came back was to make sure this doesn't happen to anyone else.
This woman found the courage to come back to court and testify against one of the men who she says beat her with everything from a chair, to a two-by-four and raped her repeatedly before she found a way to escape from this Strasberg Street in Detroit.
That nightmare only continued at a Wednesday hearing , when she claims defense attorney Gabi Silver kept badgering her on the stand insinuating that she brought this attack on herself, causing this victim to snap in court.
"I said just get to the point bitch, it slipped out, it was inappropriate... all the bottled anger" says the alleged victim.
Without a warning, she says 36th District Judge Vanessa Bradley held her in contempt and ordered her to spend three days in jail.
After our story aired Wednesday, exposing what happened - the judge seemed to have a change of heart and released her a day early.
But to make matters even worse, she says her time in a holding cell was spent right next door to her alleged attacker who she says threatened her life, claiming the suspect who is still on the loose will come back and kill her. An investigation into this matter is underway.
In the end, the judge bound suspect Curtis King over for trial. The alleged victim says she's one step closer to justice, but she hopes no other rape victim will have to go through what she did to get it.
http://www.myfoxdetroit.com/dpp/news/local/after-jail-time-for-contempt%2C-alleged-rape-victim-returns-to-testify
Sometimes you can not make the stupid stuff they do and say up
DOJ: We can force you to decrypt that laptop
The Colorado prosecution of a woman accused of a mortgage scam will test whether the government can punish you for refusing to disclose your encryption passphrase.
The Obama administration has asked a federal judge to order the defendant, Ramona Fricosu, to decrypt an encrypted laptop that police found in her bedroom during a raid of her home.
Because Fricosu has opposed the proposal, this could turn into a precedent-setting case. No U.S. appeals court appears to have ruled on whether such an order would be legal or not under the U.S. Constitution's Fifth Amendment, which broadly protects Americans' right to remain silent.
In a brief filed last Friday, Fricosu's Colorado Springs-based attorney, Philip Dubois, said defendants can't be constitutionally obligated to help the government interpret their files. "If agents execute a search warrant and find, say, a diary handwritten in code, could the target be compelled to decode, i.e., decrypt, the diary?"
To the U.S. Justice Department, though, the requested court order represents a simple extension of prosecutors' long-standing ability to assemble information that could become evidence during a trial. The department claims:
Public interests will be harmed absent requiring defendants to make available unencrypted contents in circumstances like these. Failing to compel Ms. Fricosu amounts to a concession to her and potential criminals (be it in child exploitation, national security, terrorism, financial crimes or drug trafficking cases) that encrypting all inculpatory digital evidence will serve to defeat the efforts of law enforcement officers to obtain such evidence through judicially authorized search warrants, and thus make their prosecution impossible.
Prosecutors stressed that they don't actually require the passphrase itself, meaning Fricosu would be permitted to type it in and unlock the files without anyone looking over her shoulder. They say they want only the decrypted data and are not demanding "the password to the drive, either orally or in written form."
The question of whether a criminal defendant can be legally compelled to cough up his encryption passphrase remains an unsettled one, with law review articles for at least the last 15 years arguing the merits of either approach. (A U.S. Justice Department attorney wrote an article in 1996, for instance, titled "Compelled Production of Plaintext and Keys.")
Much of the discussion has been about what analogy comes closest. Prosecutors tend to view PGP passphrases as akin to someone possessing a key to a safe filled with incriminating documents. That person can, in general, be legally compelled to hand over the key. Other examples include the U.S. Supreme Court saying that defendants can be forced to provide fingerprints, blood samples, or voice recordings.
On the other hand are civil libertarians citing other Supreme Court cases that conclude Americans can't be forced to give "compelled testimonial communications" and extending the legal shield of the Fifth Amendment to encryption passphrases. Courts already have ruled that that such protection extends to the contents of a defendant's mind, so why shouldn't a passphrase be shielded as well?
In an amicus brief (PDF) filed on Friday, the San Francisco-based Electronic Frontier Foundation argues that the Justice Department's request be rejected because of Fricosu's Fifth Amendment rights. The Fifth Amendment says that "no person...shall be compelled in any criminal case to be a witness against himself."
"Decrypting the data on the laptop can be, in and of itself, a testimonial act--revealing control over a computer and the files on it," said EFF Senior staff attorney Marcia Hofmann. "Ordering the defendant to enter an encryption password puts her in the situation the Fifth Amendment was designed to prevent: having to choose between incriminating herself, lying under oath, or risking contempt of court."
The EFF says it's interested in this case because it wants to ensure that, as computers become more portable and encrypting data becomes more commonplace, passphrases and encrypted files receive full protection under the Fifth Amendment.
Because this involves a Fifth Amendment claim, Colorado prosecutors took the unusual step of seeking approval from headquarters in Washington, D.C.: On May 5, Assistant Attorney General Lanny Breuer sent a letter to John Walsh, the U.S. Attorney for Colorado, saying "I hereby approve your request."
While the U.S. Supreme Court has not confronted the topic, a handful of lower courts have.
In March 2010, a federal judge in Michigan ruled that Thomas Kirschner, facing charges of receiving child pornography, would not have to give up his password. That's "protecting his invocation of his Fifth Amendment privilege against compelled self-incrimination," the court ruled (PDF).
A year earlier, a Vermont federal judge concluded that Sebastien Boucher, who a border guard claims had child porn on his Alienware laptop, did not have a Fifth Amendment right to keep the files encrypted. Boucher eventually complied and was convicted.
One argument published in the University of Chicago Legal Forum in 1996--constitutional arguments among legal academics have long preceded actual prosecutions--says:
The courts likely will find that compelling someone to reveal the steps necessary to decrypt a PGP-encrypted document violates the Fifth Amendment privilege against compulsory self-incrimination. Because most users protect their private keys by memorizing passwords to them and not writing them down, access to encrypted documents would almost definitely require an individual to disclose the contents of his mind. This bars the state from compelling its production. This would force law enforcement officials to grant some form of immunity to the owners of these documents to gain access to them.
Translation: One way around the Fifth Amendment is for prosecutors to offer a defendant, in this case Fricosu, immunity for what they say. But it appears as though they've stopped far short of granting her full immunity for whatever appears on the hard drive (which may not, of course, even be hers).
Fricosu was born in 1974 and living in Peyton, Colo., as of last fall. She was charged with bank fraud, wire fraud, and money laundering as part of an alleged attempt to use falsified court documents to illegally gain title to homes near Colorado Springs that were facing "imminent foreclosure" or whose owners were relocating outside the state. Some of the charges include up to 30 years in prison; she pleaded not guilty. Her husband, Scott Whatcott, was also charged.
A ruling is expected from either Magistrate Judge Michael Hegarty or District Judge Robert Blackburn.
http://news.cnet.com/8301-31921_3-20078312-281/doj-we-can-force-you-to-decrypt-that-laptop/#ixzz1SOS60QB8
"What is good for the goose is good for the gander" comes to mind or "turn about is fair play". Either saying is fit, it appears TSA does not like it when someone feels them up, but it ok when they do it.
Colo. woman accused of groping TSA agent in Ariz.
PHOENIX (AP) - Authorities say a Colorado woman who allegedly groped a female Transportation Security Administration agent at Phoenix's international airport is facing a felony count of sexual abuse.
Phoenix police say 61-year-old Yukari Mihamae is accused of grabbing the left breast of the unidentified TSA agent Thursday afternoon at an airport checkpoint.
TSA staff say Mihamae refused to be go through passenger screening and became argumentative before she squeezed and twisted the agent's breast with both hands.
Police were called and say Mihamae admitted grabbing the TSA agent and continued to argue with officers before she was arrested.
Maricopa County jail officials say Mihamae was released from custody Friday. They couldn't immediately provide any information about her case status.
Phoenix TV station KSAZ says Mihamae lives in Longmont, Colo., and is self-employed.
http://wtop.com/?nid=209&sid=2459067
After Jail Time for Contempt, Alleged Rape Victim Returns to Testify
It's already extremely hard for rape victims to come to court and testify. This alleged rape victim says the only reason she came back was to make sure this doesn't happen to anyone else.
This woman found the courage to come back to court and testify against one of the men who she says beat her with everything from a chair, to a two-by-four and raped her repeatedly before she found a way to escape from this Strasberg Street in Detroit.
That nightmare only continued at a Wednesday hearing , when she claims defense attorney Gabi Silver kept badgering her on the stand insinuating that she brought this attack on herself, causing this victim to snap in court.
"I said just get to the point bitch, it slipped out, it was inappropriate... all the bottled anger" says the alleged victim.
Without a warning, she says 36th District Judge Vanessa Bradley held her in contempt and ordered her to spend three days in jail.
After our story aired Wednesday, exposing what happened - the judge seemed to have a change of heart and released her a day early.
But to make matters even worse, she says her time in a holding cell was spent right next door to her alleged attacker who she says threatened her life, claiming the suspect who is still on the loose will come back and kill her. An investigation into this matter is underway.
In the end, the judge bound suspect Curtis King over for trial. The alleged victim says she's one step closer to justice, but she hopes no other rape victim will have to go through what she did to get it.
http://www.myfoxdetroit.com/dpp/news/local/after-jail-time-for-contempt%2C-alleged-rape-victim-returns-to-testify
Sometimes you can not make the stupid stuff they do and say up
DOJ: We can force you to decrypt that laptop
The Colorado prosecution of a woman accused of a mortgage scam will test whether the government can punish you for refusing to disclose your encryption passphrase.
The Obama administration has asked a federal judge to order the defendant, Ramona Fricosu, to decrypt an encrypted laptop that police found in her bedroom during a raid of her home.
Because Fricosu has opposed the proposal, this could turn into a precedent-setting case. No U.S. appeals court appears to have ruled on whether such an order would be legal or not under the U.S. Constitution's Fifth Amendment, which broadly protects Americans' right to remain silent.
In a brief filed last Friday, Fricosu's Colorado Springs-based attorney, Philip Dubois, said defendants can't be constitutionally obligated to help the government interpret their files. "If agents execute a search warrant and find, say, a diary handwritten in code, could the target be compelled to decode, i.e., decrypt, the diary?"
To the U.S. Justice Department, though, the requested court order represents a simple extension of prosecutors' long-standing ability to assemble information that could become evidence during a trial. The department claims:
Public interests will be harmed absent requiring defendants to make available unencrypted contents in circumstances like these. Failing to compel Ms. Fricosu amounts to a concession to her and potential criminals (be it in child exploitation, national security, terrorism, financial crimes or drug trafficking cases) that encrypting all inculpatory digital evidence will serve to defeat the efforts of law enforcement officers to obtain such evidence through judicially authorized search warrants, and thus make their prosecution impossible.
Prosecutors stressed that they don't actually require the passphrase itself, meaning Fricosu would be permitted to type it in and unlock the files without anyone looking over her shoulder. They say they want only the decrypted data and are not demanding "the password to the drive, either orally or in written form."
The question of whether a criminal defendant can be legally compelled to cough up his encryption passphrase remains an unsettled one, with law review articles for at least the last 15 years arguing the merits of either approach. (A U.S. Justice Department attorney wrote an article in 1996, for instance, titled "Compelled Production of Plaintext and Keys.")
Much of the discussion has been about what analogy comes closest. Prosecutors tend to view PGP passphrases as akin to someone possessing a key to a safe filled with incriminating documents. That person can, in general, be legally compelled to hand over the key. Other examples include the U.S. Supreme Court saying that defendants can be forced to provide fingerprints, blood samples, or voice recordings.
On the other hand are civil libertarians citing other Supreme Court cases that conclude Americans can't be forced to give "compelled testimonial communications" and extending the legal shield of the Fifth Amendment to encryption passphrases. Courts already have ruled that that such protection extends to the contents of a defendant's mind, so why shouldn't a passphrase be shielded as well?
In an amicus brief (PDF) filed on Friday, the San Francisco-based Electronic Frontier Foundation argues that the Justice Department's request be rejected because of Fricosu's Fifth Amendment rights. The Fifth Amendment says that "no person...shall be compelled in any criminal case to be a witness against himself."
"Decrypting the data on the laptop can be, in and of itself, a testimonial act--revealing control over a computer and the files on it," said EFF Senior staff attorney Marcia Hofmann. "Ordering the defendant to enter an encryption password puts her in the situation the Fifth Amendment was designed to prevent: having to choose between incriminating herself, lying under oath, or risking contempt of court."
The EFF says it's interested in this case because it wants to ensure that, as computers become more portable and encrypting data becomes more commonplace, passphrases and encrypted files receive full protection under the Fifth Amendment.
Because this involves a Fifth Amendment claim, Colorado prosecutors took the unusual step of seeking approval from headquarters in Washington, D.C.: On May 5, Assistant Attorney General Lanny Breuer sent a letter to John Walsh, the U.S. Attorney for Colorado, saying "I hereby approve your request."
While the U.S. Supreme Court has not confronted the topic, a handful of lower courts have.
In March 2010, a federal judge in Michigan ruled that Thomas Kirschner, facing charges of receiving child pornography, would not have to give up his password. That's "protecting his invocation of his Fifth Amendment privilege against compelled self-incrimination," the court ruled (PDF).
A year earlier, a Vermont federal judge concluded that Sebastien Boucher, who a border guard claims had child porn on his Alienware laptop, did not have a Fifth Amendment right to keep the files encrypted. Boucher eventually complied and was convicted.
One argument published in the University of Chicago Legal Forum in 1996--constitutional arguments among legal academics have long preceded actual prosecutions--says:
The courts likely will find that compelling someone to reveal the steps necessary to decrypt a PGP-encrypted document violates the Fifth Amendment privilege against compulsory self-incrimination. Because most users protect their private keys by memorizing passwords to them and not writing them down, access to encrypted documents would almost definitely require an individual to disclose the contents of his mind. This bars the state from compelling its production. This would force law enforcement officials to grant some form of immunity to the owners of these documents to gain access to them.
Translation: One way around the Fifth Amendment is for prosecutors to offer a defendant, in this case Fricosu, immunity for what they say. But it appears as though they've stopped far short of granting her full immunity for whatever appears on the hard drive (which may not, of course, even be hers).
Fricosu was born in 1974 and living in Peyton, Colo., as of last fall. She was charged with bank fraud, wire fraud, and money laundering as part of an alleged attempt to use falsified court documents to illegally gain title to homes near Colorado Springs that were facing "imminent foreclosure" or whose owners were relocating outside the state. Some of the charges include up to 30 years in prison; she pleaded not guilty. Her husband, Scott Whatcott, was also charged.
A ruling is expected from either Magistrate Judge Michael Hegarty or District Judge Robert Blackburn.
http://news.cnet.com/8301-31921_3-20078312-281/doj-we-can-force-you-to-decrypt-that-laptop/#ixzz1SOS60QB8
"What is good for the goose is good for the gander" comes to mind or "turn about is fair play". Either saying is fit, it appears TSA does not like it when someone feels them up, but it ok when they do it.
Colo. woman accused of groping TSA agent in Ariz.
PHOENIX (AP) - Authorities say a Colorado woman who allegedly groped a female Transportation Security Administration agent at Phoenix's international airport is facing a felony count of sexual abuse.
Phoenix police say 61-year-old Yukari Mihamae is accused of grabbing the left breast of the unidentified TSA agent Thursday afternoon at an airport checkpoint.
TSA staff say Mihamae refused to be go through passenger screening and became argumentative before she squeezed and twisted the agent's breast with both hands.
Police were called and say Mihamae admitted grabbing the TSA agent and continued to argue with officers before she was arrested.
Maricopa County jail officials say Mihamae was released from custody Friday. They couldn't immediately provide any information about her case status.
Phoenix TV station KSAZ says Mihamae lives in Longmont, Colo., and is self-employed.
http://wtop.com/?nid=209&sid=2459067
Saturday, July 16, 2011
Saturday 07-16-11
Better pay attention boys and girls this is a smart man and a good economist.
Return of the Gold Standard as world order unravels
by Ambrose Evans-Pritchard
As the twin pillars of international monetary system threaten to come tumbling down in unison, gold has reclaimed its ancient status as the anchor of stability. The spot price surged to an all-time high of $1,594 an ounce in London, lifting silver to $39 in its train.
On one side of the Atlantic, the eurozone debt crisis has spread to the countries that may be too big to save - Spain and Italy - though RBS thinks a €3.5 trillion rescue fund would ensure survival of Europe's currency union.
On the other side, the recovery has sputtered out and the printing presses are being oiled again. Brinkmanship between the Congress and the White House over the US debt ceiling has compelled Moody's to warn of a "very small but rising risk" that the world's paramount power may default within two weeks. "The unthinkable is now thinkable," said Ross Norman, director of thebulliondesk.com.
Fed chair Ben Bernanke confessed to Congress that growth has failed to gain traction. "Deflationary risks might re-emerge, implying a need for additional policy support," he said.
The bar to QE3 - yet more bond purchases - is even lower than markets had thought. The new intake of hard-money men on the voting committee has not shifted Fed thinking, despite global anger at dollar debasement under QE2.
Fuelling the blaze, the emerging powers of Asia are almost all running uber-loose monetary policies. Most have negative real interest rates that push citizens out of bank accounts and into gold, or property. China is an arch-inflater. Prices are rising at 6.4pc, yet the one-year deposit rate is just 3.5pc. India's central bank is far behind the curve.
"It is very scary: the flight to gold is accelerating at a faster and faster speed," said Peter Hambro, chairman of Britain's biggest pure gold listing Petropavlovsk.
"One of the big US banks texted me today to say that if QE3 actually happens, we could see gold at $5,000 and silver at $1,000. I feel terribly sorry for anybody on fixed incomes tied to a fiat currency because they are not going to be able to buy things with that paper money."
China, Russia, Brazil, India, the Mid-East petro-powers have diversified their $7 trillion reserves into euros over the last decade to limit dollar exposure. As Europe's monetary union itself faces an existential crisis, there is no other safe-haven currency able to absorb the flows. The Swiss franc, Canada's loonie, the Aussie, and Korea's won are too small.
"There is no depth of market in these other currencies, so gold is the obvious play," said Neil Mellor from BNY Mellon. Western central banks (though not the US, Germany, or Italy) sold much of their gold at the depths of the bear market a decade ago. The Bank of England wins the booby prize for selling into the bottom at €254 an ounce on Gordon Brown's orders in 1999. But Russia, China, India, the Gulf states, the Philippines, and Kazakhstan have been buying.
China is coy, revealing purchases with a long delay. It has admitted to doubling its gold reserves to 1,054 tonnes or $54bn. This is just a tiny sliver of its $3.2 trillion reserves. China's Chamber of Commerce said this should be raised eightfold to 8,000 tonnes.
Xia Bin, an adviser to China's central bank, said in June that the country's reserve strategy needs an "urgent" overhaul. Instead of buying paper IOU's from a prostrate West, China should invest in strategic assets and accumulate gold by "buying the dips".
Step by step, the world is edging towards a revived Gold Standard as it becomes clearer that Japan and the West have reached debt saturation. World Bank chief Robert Zoellick said it was time to "consider employing gold as an international reference point." The Swiss parliament is to hold hearings on a parallel "Gold Franc". Utah has recognised gold as legal tender for tax payments.
A new Gold Standard would probably be based on a variant of the 'Bancor' proposed by Keynes in the late 1940s. This was a basket of 30 commodities intended to be less deflationary than pure gold, which had compounded in the Great Depression. The idea was revived by China's central bank chief Zhou Xiaochuan two years ago as a way of curbing the "credit-based" excess.
Mr Bernanke himself was grilled by Congress this week on the role of gold. Why do people by gold? "As protection against of what we call tail risks: really, really bad outcomes," he replied.
Indeed.
http://www.telegraph.co.uk/finance/comment/ambroseevans_pritchard/8638644/Return-of-the-Gold-Standard-as-world-order-unravels.html
What a bunch, they need to get a clue. Political correctness is ruining the country.
94-year-old upset by TSA pat down
RALEIGH (WTVD) -- A 94-year-old wheelchair-bound Florida woman says a search she went through at Raleigh/Durham International Airport went too far.
Marian Peterson said it happened July 6 as she went through a TSA security checkpoint before boarding a flight home.
Peterson said she was selected for extra screening. First, security officers lifted her out of her wheelchair and helped her stand in a full body scanner. Then, she was given a physical pat down.
"They took me to one side and they patted me down, and they made me stand for, with my arms out, for over 10 minutes," she said. "I was beginning to feel that I wasn't going to be able to continue to stand, I was going to fall down or something."
"I asked, I said why are you doing this, and the woman was very polite and said 'I don't know, maybe the scanner detected something or maybe she moved,'" recalled Peterson's daughter Marian Malone.
Peterson's family said it's not just the length of the search they object to, it's the way it was done.
"She said it would be in-depth. She started the putdown, and at that point, she asked mom to spread her legs. She stood there with her legs spread and she checked every place thoroughly," said Malone.
"They groped her. All of her body. Her crotch, her breasts. And everything else," said son Joe Peterson.
The Petersons said the search seemed unnecessary given Marian's obvious age.
"I didn't think I was much of a threat to anybody," said Marian Peterson.
"My sister had even asked them, you know, what did she do? Why are we doing this? What's going on here," said Joe Peterson.
Contacted by ABC11's Jacksonville, FL sister station, a Transportation Security Administration spokesperson issued the following statement:
"While every person and item must be screened before entering the secure boarding area, TSA works with passengers to resolve security alarms in a respectful and sensitive manner."
But the Petersons say they don't feel the search was handled in a sensitive manner and that while they think security at airports is very important, they should be sensitive to certain passengers.
"I thought it was totally uncalled for. I think if it was absolutely necessary, that they should've taken her in a private area, and I think it was uncalled for," said Malone. "It just was not being thoughtful for an elderly person."
TSA is expected to begin a pilot program this fall that will try more "risk based" screening. It will start with just Delta and American at four U.S. airports. Raleigh is not included.
http://abclocal.go.com/wtvd/story?section=news/local&id=8250625
They are pround it is under 1 percent, but really they have no clue what it is because they are so inept. Listen to this report is almost unbelievable.
http://media.dev-cms.com/wtop/21/2198/219835.mp3
Return of the Gold Standard as world order unravels
by Ambrose Evans-Pritchard
As the twin pillars of international monetary system threaten to come tumbling down in unison, gold has reclaimed its ancient status as the anchor of stability. The spot price surged to an all-time high of $1,594 an ounce in London, lifting silver to $39 in its train.
On one side of the Atlantic, the eurozone debt crisis has spread to the countries that may be too big to save - Spain and Italy - though RBS thinks a €3.5 trillion rescue fund would ensure survival of Europe's currency union.
On the other side, the recovery has sputtered out and the printing presses are being oiled again. Brinkmanship between the Congress and the White House over the US debt ceiling has compelled Moody's to warn of a "very small but rising risk" that the world's paramount power may default within two weeks. "The unthinkable is now thinkable," said Ross Norman, director of thebulliondesk.com.
Fed chair Ben Bernanke confessed to Congress that growth has failed to gain traction. "Deflationary risks might re-emerge, implying a need for additional policy support," he said.
The bar to QE3 - yet more bond purchases - is even lower than markets had thought. The new intake of hard-money men on the voting committee has not shifted Fed thinking, despite global anger at dollar debasement under QE2.
Fuelling the blaze, the emerging powers of Asia are almost all running uber-loose monetary policies. Most have negative real interest rates that push citizens out of bank accounts and into gold, or property. China is an arch-inflater. Prices are rising at 6.4pc, yet the one-year deposit rate is just 3.5pc. India's central bank is far behind the curve.
"It is very scary: the flight to gold is accelerating at a faster and faster speed," said Peter Hambro, chairman of Britain's biggest pure gold listing Petropavlovsk.
"One of the big US banks texted me today to say that if QE3 actually happens, we could see gold at $5,000 and silver at $1,000. I feel terribly sorry for anybody on fixed incomes tied to a fiat currency because they are not going to be able to buy things with that paper money."
China, Russia, Brazil, India, the Mid-East petro-powers have diversified their $7 trillion reserves into euros over the last decade to limit dollar exposure. As Europe's monetary union itself faces an existential crisis, there is no other safe-haven currency able to absorb the flows. The Swiss franc, Canada's loonie, the Aussie, and Korea's won are too small.
"There is no depth of market in these other currencies, so gold is the obvious play," said Neil Mellor from BNY Mellon. Western central banks (though not the US, Germany, or Italy) sold much of their gold at the depths of the bear market a decade ago. The Bank of England wins the booby prize for selling into the bottom at €254 an ounce on Gordon Brown's orders in 1999. But Russia, China, India, the Gulf states, the Philippines, and Kazakhstan have been buying.
China is coy, revealing purchases with a long delay. It has admitted to doubling its gold reserves to 1,054 tonnes or $54bn. This is just a tiny sliver of its $3.2 trillion reserves. China's Chamber of Commerce said this should be raised eightfold to 8,000 tonnes.
Xia Bin, an adviser to China's central bank, said in June that the country's reserve strategy needs an "urgent" overhaul. Instead of buying paper IOU's from a prostrate West, China should invest in strategic assets and accumulate gold by "buying the dips".
Step by step, the world is edging towards a revived Gold Standard as it becomes clearer that Japan and the West have reached debt saturation. World Bank chief Robert Zoellick said it was time to "consider employing gold as an international reference point." The Swiss parliament is to hold hearings on a parallel "Gold Franc". Utah has recognised gold as legal tender for tax payments.
A new Gold Standard would probably be based on a variant of the 'Bancor' proposed by Keynes in the late 1940s. This was a basket of 30 commodities intended to be less deflationary than pure gold, which had compounded in the Great Depression. The idea was revived by China's central bank chief Zhou Xiaochuan two years ago as a way of curbing the "credit-based" excess.
Mr Bernanke himself was grilled by Congress this week on the role of gold. Why do people by gold? "As protection against of what we call tail risks: really, really bad outcomes," he replied.
Indeed.
http://www.telegraph.co.uk/finance/comment/ambroseevans_pritchard/8638644/Return-of-the-Gold-Standard-as-world-order-unravels.html
What a bunch, they need to get a clue. Political correctness is ruining the country.
94-year-old upset by TSA pat down
RALEIGH (WTVD) -- A 94-year-old wheelchair-bound Florida woman says a search she went through at Raleigh/Durham International Airport went too far.
Marian Peterson said it happened July 6 as she went through a TSA security checkpoint before boarding a flight home.
Peterson said she was selected for extra screening. First, security officers lifted her out of her wheelchair and helped her stand in a full body scanner. Then, she was given a physical pat down.
"They took me to one side and they patted me down, and they made me stand for, with my arms out, for over 10 minutes," she said. "I was beginning to feel that I wasn't going to be able to continue to stand, I was going to fall down or something."
"I asked, I said why are you doing this, and the woman was very polite and said 'I don't know, maybe the scanner detected something or maybe she moved,'" recalled Peterson's daughter Marian Malone.
Peterson's family said it's not just the length of the search they object to, it's the way it was done.
"She said it would be in-depth. She started the putdown, and at that point, she asked mom to spread her legs. She stood there with her legs spread and she checked every place thoroughly," said Malone.
"They groped her. All of her body. Her crotch, her breasts. And everything else," said son Joe Peterson.
The Petersons said the search seemed unnecessary given Marian's obvious age.
"I didn't think I was much of a threat to anybody," said Marian Peterson.
"My sister had even asked them, you know, what did she do? Why are we doing this? What's going on here," said Joe Peterson.
Contacted by ABC11's Jacksonville, FL sister station, a Transportation Security Administration spokesperson issued the following statement:
"While every person and item must be screened before entering the secure boarding area, TSA works with passengers to resolve security alarms in a respectful and sensitive manner."
But the Petersons say they don't feel the search was handled in a sensitive manner and that while they think security at airports is very important, they should be sensitive to certain passengers.
"I thought it was totally uncalled for. I think if it was absolutely necessary, that they should've taken her in a private area, and I think it was uncalled for," said Malone. "It just was not being thoughtful for an elderly person."
TSA is expected to begin a pilot program this fall that will try more "risk based" screening. It will start with just Delta and American at four U.S. airports. Raleigh is not included.
http://abclocal.go.com/wtvd/story?section=news/local&id=8250625
They are pround it is under 1 percent, but really they have no clue what it is because they are so inept. Listen to this report is almost unbelievable.
http://media.dev-cms.com/wtop/21/2198/219835.mp3
Friday, July 15, 2011
Friday 07-15-11
I use a regular cell phone, but i guess it would be good to know or at least have an idea of how much you use. The there is an online app under the article that lets you pick between a phone and laptop.
The apps that eat your wireless data
NEW YORK (AP) - If you have a cellphone with a monthly limit on how much data you can use, here are some tips on what types of phone use will gobble up your precious megabytes:
_ Streaming video and videoconferencing. The biggest offender. One minute of YouTube-quality video eats up 2 megabytes. If you're on a plan that gives you 200 megabytes per month, you can't even watch Lady Gaga's "Telephone" video once per day. If you're on a 2 gigabyte plan you can, but don't make your iPhone a replacement for a TV. In either case, it's fine to indulge in YouTube and Netflix if you're on Wi-Fi.
_ Streaming audio. The second biggest offender, and potentially more serious. While video is something we need to see to enjoy, Internet radio is more of an accompaniment to other activities, such as jogging or doing dishes. That means some people like to keep it on for hours. Audio consumes about a quarter of the data that video does, but 10 minutes a day will break the bank if you're on a 200 megabyte plan. One hour a day of Pandora consumes nearly a gigabyte, which you can afford if you're on a 2-gigabyte plan and don't use other data-hogging apps.
_ Photos. If you're a real shutterbug, photos can consume significant amounts of data. Sending and viewing photos both count toward your monthly limit. Posting 10 photos per day eats up most of a 200 megabyte plan. If you're on a 2-gigabyte plan, you probably don't have to worry about photos.
_ Maps. Navigation apps consume lots of data when they retrieve map images, up to a megabyte a minute. You're also likely to use them for long periods of time when you're away from Wi-Fi, such as when you're driving. Watch out for these.
_ Web surfing. Web pages vary widely in size, so this will depend quite a bit on whether you like to visit graphically rich sites (lots of data) or spare, text-oriented ones (less data). But roughly speaking, ten pages a day will eat up about half of a 200 megabyte plan. Again, those on 2-gigabyte plans don't need to worry much about surfing.
_ Facebook. Roughly equivalent to Web surfing. Status updates won't take much data, but sending photos and viewing friends' pictures will.
_ Email. Most emails are tiny, in terms of data. Basically, you can send and receive email all you want, as long as they don't have attachments such as photos.
_ Twitter. Like email, these short messages don't use much data, but if you follow a lot of people and click on links, usage adds up.
_ Weather apps. Small, focused apps that report simple but useful things, such as the weather forecast, save data (and time) compared with looking up the same information on a Web page.
http://wtop.com/?nid=256&sid=2447714
Here is a computer app that will help you calculate your usage.
http://www.att.com/standalone/data-calculator/
A parent arrested for trying to keep the TSA from feeling up her teenage daughter, what is the matter with these people. There are hearings (or i should political posturing) happening on capital hill, nothing will come of it, they all (most) are movie stars now.
Clarksville mom arrested at airport over child's security screening
A Clarksville mother allegedly lashed out at airport security agents Saturday when they attempted to pat down her teenage daughter.
In an arrest report, police at the Nashville International Airport said Andrea Abbott refused to allow security guards to pat down her teenage daughter. Police said Abbott feared her daughter would be "touched inappropriately."
Authorities said Abbott eventually allowed the pat down but then tried to take cell phone video and started yelling when authorities asked her to stop.
Officers charged Abbot with disorderly conduct. She was transported to the Metro Jail. Her bond was set at $1,000.
http://www.theleafchronicle.com/article/20110713/NEWS01/107130345/1002/rss

Gerald Celente - Expect Bank Holiday & Economic Martial Law
Gerald Celente informed King World News today that he expects a bank holiday to happen. Here is a portion of the KWN exclusive detailed sneak peak at the upcoming Summer Trends Journal, “What will another major terror strike mean should an attack hit one of the major NATO nations? The effects this time will go global. Bank holidays will be called, the US and other fragile economies will crumble, gold and silver will soar and already troubled currencies will crash. Economic martial law will be declared, promised as a temporary measure, once in place it will remain in place.”
Celente continues:
“Civil rights will be suspended and particularly in America, Homeland Security, already intrusive, will achieve an Orwellian omnipresence. With banks closed and economic martial law in place, restrictions will be set on the amounts, times and frequencies of withdrawals (of cash). It will be essential to have a stash of cash on hand.”
When asked to comment on the above portion of his upcoming Summer Trends Journal Celente stated, “Let’s listen to what Moammar Gaddafi said recently, he said they are planning revenge attacks against Nato countries that are trying to kill him...And you’ve heard me say this before, if his major export in Libya was broccoli you think anybody would be there?
It couldn’t be because of the sweet crude oil that the Europeans buy from him...So when they start retaliating, when terror strikes, the people will again rally around the government, they will get more of their rights taken away from them, and as they get their rights taken away from them they’ll get their money taken away from them too.
They’ve done it before, they’ll do it again. Go back to 1933, the emergency banking act under FDR, what did they do? They called a bank holiday. You can’t get your money out and oh by the way turn in all of your gold. Sell us your gold at $20.65 an ounce and after we get it all we are going to repeg the price of gold to $35 an ounce, which means back in those days when the dollar was pegged to gold you just lost 40% of your purchasing power.
I believe the same thing is going to happen now because they are going to devalue the currencies as a means of paying off all of this worthless debt.”
http://kingworldnews.com/kingworldnews/KWN_DailyWeb/Entries/2011/7/7_Gerald_Celente_-_Expect_Bank_Holiday_&_Economic_Martial_Law.html
The apps that eat your wireless data
NEW YORK (AP) - If you have a cellphone with a monthly limit on how much data you can use, here are some tips on what types of phone use will gobble up your precious megabytes:
_ Streaming video and videoconferencing. The biggest offender. One minute of YouTube-quality video eats up 2 megabytes. If you're on a plan that gives you 200 megabytes per month, you can't even watch Lady Gaga's "Telephone" video once per day. If you're on a 2 gigabyte plan you can, but don't make your iPhone a replacement for a TV. In either case, it's fine to indulge in YouTube and Netflix if you're on Wi-Fi.
_ Streaming audio. The second biggest offender, and potentially more serious. While video is something we need to see to enjoy, Internet radio is more of an accompaniment to other activities, such as jogging or doing dishes. That means some people like to keep it on for hours. Audio consumes about a quarter of the data that video does, but 10 minutes a day will break the bank if you're on a 200 megabyte plan. One hour a day of Pandora consumes nearly a gigabyte, which you can afford if you're on a 2-gigabyte plan and don't use other data-hogging apps.
_ Photos. If you're a real shutterbug, photos can consume significant amounts of data. Sending and viewing photos both count toward your monthly limit. Posting 10 photos per day eats up most of a 200 megabyte plan. If you're on a 2-gigabyte plan, you probably don't have to worry about photos.
_ Maps. Navigation apps consume lots of data when they retrieve map images, up to a megabyte a minute. You're also likely to use them for long periods of time when you're away from Wi-Fi, such as when you're driving. Watch out for these.
_ Web surfing. Web pages vary widely in size, so this will depend quite a bit on whether you like to visit graphically rich sites (lots of data) or spare, text-oriented ones (less data). But roughly speaking, ten pages a day will eat up about half of a 200 megabyte plan. Again, those on 2-gigabyte plans don't need to worry much about surfing.
_ Facebook. Roughly equivalent to Web surfing. Status updates won't take much data, but sending photos and viewing friends' pictures will.
_ Email. Most emails are tiny, in terms of data. Basically, you can send and receive email all you want, as long as they don't have attachments such as photos.
_ Twitter. Like email, these short messages don't use much data, but if you follow a lot of people and click on links, usage adds up.
_ Weather apps. Small, focused apps that report simple but useful things, such as the weather forecast, save data (and time) compared with looking up the same information on a Web page.
http://wtop.com/?nid=256&sid=2447714
Here is a computer app that will help you calculate your usage.
http://www.att.com/standalone/data-calculator/
A parent arrested for trying to keep the TSA from feeling up her teenage daughter, what is the matter with these people. There are hearings (or i should political posturing) happening on capital hill, nothing will come of it, they all (most) are movie stars now.
Clarksville mom arrested at airport over child's security screening
A Clarksville mother allegedly lashed out at airport security agents Saturday when they attempted to pat down her teenage daughter.
In an arrest report, police at the Nashville International Airport said Andrea Abbott refused to allow security guards to pat down her teenage daughter. Police said Abbott feared her daughter would be "touched inappropriately."
Authorities said Abbott eventually allowed the pat down but then tried to take cell phone video and started yelling when authorities asked her to stop.
Officers charged Abbot with disorderly conduct. She was transported to the Metro Jail. Her bond was set at $1,000.
http://www.theleafchronicle.com/article/20110713/NEWS01/107130345/1002/rss

Gerald Celente - Expect Bank Holiday & Economic Martial Law
Gerald Celente informed King World News today that he expects a bank holiday to happen. Here is a portion of the KWN exclusive detailed sneak peak at the upcoming Summer Trends Journal, “What will another major terror strike mean should an attack hit one of the major NATO nations? The effects this time will go global. Bank holidays will be called, the US and other fragile economies will crumble, gold and silver will soar and already troubled currencies will crash. Economic martial law will be declared, promised as a temporary measure, once in place it will remain in place.”
Celente continues:
“Civil rights will be suspended and particularly in America, Homeland Security, already intrusive, will achieve an Orwellian omnipresence. With banks closed and economic martial law in place, restrictions will be set on the amounts, times and frequencies of withdrawals (of cash). It will be essential to have a stash of cash on hand.”
When asked to comment on the above portion of his upcoming Summer Trends Journal Celente stated, “Let’s listen to what Moammar Gaddafi said recently, he said they are planning revenge attacks against Nato countries that are trying to kill him...And you’ve heard me say this before, if his major export in Libya was broccoli you think anybody would be there?
It couldn’t be because of the sweet crude oil that the Europeans buy from him...So when they start retaliating, when terror strikes, the people will again rally around the government, they will get more of their rights taken away from them, and as they get their rights taken away from them they’ll get their money taken away from them too.
They’ve done it before, they’ll do it again. Go back to 1933, the emergency banking act under FDR, what did they do? They called a bank holiday. You can’t get your money out and oh by the way turn in all of your gold. Sell us your gold at $20.65 an ounce and after we get it all we are going to repeg the price of gold to $35 an ounce, which means back in those days when the dollar was pegged to gold you just lost 40% of your purchasing power.
I believe the same thing is going to happen now because they are going to devalue the currencies as a means of paying off all of this worthless debt.”
http://kingworldnews.com/kingworldnews/KWN_DailyWeb/Entries/2011/7/7_Gerald_Celente_-_Expect_Bank_Holiday_&_Economic_Martial_Law.html
Thursday, July 14, 2011
Thursday 07-14-11
Army Ranger receives Medal of Honor from Obama
At the White House today, Army Ranger Sergeant Leroy Petry became only the second living service member to be presented with the military's highest decoration -- the Medal of Honor.
In Afghanistan. Poetry was shot in both legs and then lost a hand while throwing an enemy grenade away from himself and two fellow Army Rangers - all the while continuing to call out orders so that his unit could fulfill its mission, according to soldiers who served with him. President Obama presented Petry with the award.
http://www.federalnewsradio.com/?nid=17&sid=2455349
I saw the following link on the Survival Blog, really neat site with a ton of info.
http://www.ces.org.za/
It is worth looking at, in the past i have written several time (and posted articles about) alternative currencies. This is what they say about themselves.
If you believe the following (about the police threading lightly) i have a bridge to sell you at a good price
Smile, You're On Everyone's Camera
According to the Wall Street Journal, police departments across the nation will soon adopt handheld facial-recognition systems that will let them identify people with a snapshot. These new capabilities are made possible by BI2 Technologies, a Massachusetts company that has developed a small device that attaches to officers' iPhones. The police departments who spoke to the Journal said they plan to use the device only when officers suspect criminal activity and have no other way to identify a person—for instance, when they stop a driver who isn't carrying her license. Law enforcement officials also seemed wary about civil liberties concerns. Is snapping someone's photo from five feet away considered a search? Courts haven't decided the issue, but sheriffs who spoke to the paper say they plan to exercise caution.
Don't believe it. Soon, face recognition will be ubiquitous. While the police may promise to tread lightly, the technology is likely to become so good, so quickly that officers will find themselves reaching for their cameras in all kinds of situations. The police will still likely use traditional ID technologies like fingerprinting—or even iris scanning—as these are generally more accurate than face-scanning, but face-scanning has an obvious advantage over fingerprints: It works from far away. Bunch of guys loitering on the corner? Scantily clad woman hanging around that run-down motel? Two dudes who look like they're smoking a funny-looking cigarette? Why not snap them all just to make sure they're on the up-and-up?
Sure, this isn't a new worry. Early in 2001, police scanned the faces of people going to the Super Bowl, and officials rolled out the technology at Logan Airport in Boston after 9/11. Those efforts raised a stink, and the authorities decided to pull back. But society has changed profoundly in the last decade, and face recognition is now set to go mainstream. What's more, the police may be the least of your worries. In the coming years—if not months—we'll see a slew of apps that allow your friends and neighbors to snap your face and get your name and other information you've put online. This isn't a theoretical worry; the technology exists, now, to do this sort of thing crudely, and the only thing stopping companies from deploying it widely is a fear of public outcry. That fear won't last long. Face recognition for everyone is coming. Get used to it.
What's changed in the last decade? Three things. First, computers have gotten better at recognizing faces. The technology works by analyzing dozens of different features—the distance between your eyes, the width of your nose—that remain the same across photographs. As computers have gotten faster and digital photography has gotten better, face recognition has filtered down to consumer photo software. (I find Picasa to be uncannily good). By this point, every tech giant has snapped up face-identifying expertise. Apple purchased the face-recognition firm Polar Rose last year. In 2006, Google acquired the biometric recognition company Neven Vision, and Hartmut Neven, one of the world's experts in computer vision, is a respected engineer at the company. A Microsoft research team in Israel has built a fantastic app that uses face-recognition systems to search the Web for pictures of people who are in your photo album. And last year Facebook rolled out a tool that automatically suggests names of people to tag in your pictures.
Another major factor that augurs the face-recognition era is that we've become accustomed to ubiquitous photography. Now that we all carry cameras everywhere, it no longer seems odd when someone points a lens in your direction—you probably don't even notice it. Indeed, we all have a general expectation that if we go outside, someone is going to capture our image. We might not like it, but we live with it.
Finally, there's Facebook. Ten years ago we were worried about authorities building a worldwide database of our faces. In 2004, a Harvard student built a site that let people post their own names and faces, and hundreds of millions of people around the world have taken him up on it. We're all posting pictures, and tagging names to pictures, at a furious rate—according to Facebook, people add 100 million names to faces on Facebook every day. The face-recognition tools available to law enforcement agencies will match you against government databases—the DMV or passport database, or the FBI's most-wanted list—but the technology available to consumers will be able to do just as well by matching your face to online snapshots. The government couldn't have built a better facial database if it tried. (See the Onion's video, "CIA's 'Facebook' Program Dramatically Cut Agency's Costs.")
So, when will consumer tech companies get over their fears of bringing out a mainstream face-recognition app? In May, Eric Schmidt, Google's executive chairman, told an audience at the D9 conference that the company had decided not to put out a face-recognition tool out of fear it would be misused. People at Google have indeed confirmed to me that the company has no current plans to release such a system. In fact, Google has gone out of its way to prevent face-recognition in its apps. Google Goggles—the smart-phone app that returns information from the Web when you take a photo of an everyday item—doesn't work on faces. But that's not because it can't work on faces. Google engineers have publicly admitted that, in prototypes, the system is really good at identifying faces. At a conference last year, Google engineer David Petrou said that the system is capable of identifying the face of someone who has as few as 17 other pictures online.* If there are 50 photos, Goggles will be able to get your name almost every time. "We do it well, but it's not deployed," Petrous said.
But Google won't have that luxury forever. Google reps have told me that face-recognition is something that Goggles users have asked for. This isn't surprising—such a tool would be incredibly useful. If you meet someone at a conference, you could point your camera their way and get their contact info. You could snap a group photo at your family reunion and have the pictures automatically filed by name in your photo album. Or you could think of it as Shazam for strangers—who is that woman who's always winking at you on the bus, or that creepy fellow who's leering at you from across the bar? Snap their pictures and find out. Given the demand, and given the widespread availability of the technology, it's inevitable that some company will release such a face-recognition tool very soon. And once the horse leaves the barn, it will become socially acceptable for Google and other tech giants to follow.
What about the privacy fears? What of the possibility that the police will use face-recognition systems to conduct illegal searches, or that con men will use them to find victims, or that, more fundamentally, they'll erase our last shreds of anonymity? These are all legitimate concerns, and indications of how much more annoying (and maybe even terrifying) the world will be to navigate in the face-recognition age. But pointing out the potential abuses of this software—and surely there will be a media outcry—won't make it go away. Technology marches forward and ordinary people—people who will be stalked, thrown in jail, or otherwise harassed on the basis of a facial identified—will be collateral damage.
Soon, though, we'll all learn to live with it. Etiquette and even regulations will develop around when it's OK to point your camera at someone and get her name. It's too late to turn back now: If your face and your name are online today, you've already made yourself searchable. Face-recognition systems simply turn the search on its head—instead of looking for your picture by typing in your name, I can now search for your name by snapping your picture. Don't want yourself searchable, period? You can always get off the Internet, or always leave the house wearing a funny hat and a fake nose.
http://www.slate.com/id/2299134/?from=rss
http://www.slate.com/id/2299134/pagenum/2
At the White House today, Army Ranger Sergeant Leroy Petry became only the second living service member to be presented with the military's highest decoration -- the Medal of Honor.
In Afghanistan. Poetry was shot in both legs and then lost a hand while throwing an enemy grenade away from himself and two fellow Army Rangers - all the while continuing to call out orders so that his unit could fulfill its mission, according to soldiers who served with him. President Obama presented Petry with the award.
http://www.federalnewsradio.com/?nid=17&sid=2455349
I saw the following link on the Survival Blog, really neat site with a ton of info.
http://www.ces.org.za/
It is worth looking at, in the past i have written several time (and posted articles about) alternative currencies. This is what they say about themselves.
With the impending implosion of the usury-based, global money system, now is the time to seek a new way of 'doing' money, one not based on debt and controlled by a global monetary elite that seems happy about destroying our planet in the pursuit of profit.
Conventional money is created as debt by private financial institutions for their own profit-making purposes, not as a public service. This is the root cause of the economic, social and environmental problems that beset us. The amount of debt determines the quantity of money, which has nothing to do with the amount of money we need to live decent lives.
CES money is 'created' by its users so it can never be in short supply. So long as you can offer something of value you can have from the community goods and services of like value.
Join the growing community who have discovered a new way of 'doing' money, a healthy money that will create a healthy society.
If you believe the following (about the police threading lightly) i have a bridge to sell you at a good price
Smile, You're On Everyone's Camera
According to the Wall Street Journal, police departments across the nation will soon adopt handheld facial-recognition systems that will let them identify people with a snapshot. These new capabilities are made possible by BI2 Technologies, a Massachusetts company that has developed a small device that attaches to officers' iPhones. The police departments who spoke to the Journal said they plan to use the device only when officers suspect criminal activity and have no other way to identify a person—for instance, when they stop a driver who isn't carrying her license. Law enforcement officials also seemed wary about civil liberties concerns. Is snapping someone's photo from five feet away considered a search? Courts haven't decided the issue, but sheriffs who spoke to the paper say they plan to exercise caution.
Don't believe it. Soon, face recognition will be ubiquitous. While the police may promise to tread lightly, the technology is likely to become so good, so quickly that officers will find themselves reaching for their cameras in all kinds of situations. The police will still likely use traditional ID technologies like fingerprinting—or even iris scanning—as these are generally more accurate than face-scanning, but face-scanning has an obvious advantage over fingerprints: It works from far away. Bunch of guys loitering on the corner? Scantily clad woman hanging around that run-down motel? Two dudes who look like they're smoking a funny-looking cigarette? Why not snap them all just to make sure they're on the up-and-up?
Sure, this isn't a new worry. Early in 2001, police scanned the faces of people going to the Super Bowl, and officials rolled out the technology at Logan Airport in Boston after 9/11. Those efforts raised a stink, and the authorities decided to pull back. But society has changed profoundly in the last decade, and face recognition is now set to go mainstream. What's more, the police may be the least of your worries. In the coming years—if not months—we'll see a slew of apps that allow your friends and neighbors to snap your face and get your name and other information you've put online. This isn't a theoretical worry; the technology exists, now, to do this sort of thing crudely, and the only thing stopping companies from deploying it widely is a fear of public outcry. That fear won't last long. Face recognition for everyone is coming. Get used to it.
What's changed in the last decade? Three things. First, computers have gotten better at recognizing faces. The technology works by analyzing dozens of different features—the distance between your eyes, the width of your nose—that remain the same across photographs. As computers have gotten faster and digital photography has gotten better, face recognition has filtered down to consumer photo software. (I find Picasa to be uncannily good). By this point, every tech giant has snapped up face-identifying expertise. Apple purchased the face-recognition firm Polar Rose last year. In 2006, Google acquired the biometric recognition company Neven Vision, and Hartmut Neven, one of the world's experts in computer vision, is a respected engineer at the company. A Microsoft research team in Israel has built a fantastic app that uses face-recognition systems to search the Web for pictures of people who are in your photo album. And last year Facebook rolled out a tool that automatically suggests names of people to tag in your pictures.
Another major factor that augurs the face-recognition era is that we've become accustomed to ubiquitous photography. Now that we all carry cameras everywhere, it no longer seems odd when someone points a lens in your direction—you probably don't even notice it. Indeed, we all have a general expectation that if we go outside, someone is going to capture our image. We might not like it, but we live with it.
Finally, there's Facebook. Ten years ago we were worried about authorities building a worldwide database of our faces. In 2004, a Harvard student built a site that let people post their own names and faces, and hundreds of millions of people around the world have taken him up on it. We're all posting pictures, and tagging names to pictures, at a furious rate—according to Facebook, people add 100 million names to faces on Facebook every day. The face-recognition tools available to law enforcement agencies will match you against government databases—the DMV or passport database, or the FBI's most-wanted list—but the technology available to consumers will be able to do just as well by matching your face to online snapshots. The government couldn't have built a better facial database if it tried. (See the Onion's video, "CIA's 'Facebook' Program Dramatically Cut Agency's Costs.")
So, when will consumer tech companies get over their fears of bringing out a mainstream face-recognition app? In May, Eric Schmidt, Google's executive chairman, told an audience at the D9 conference that the company had decided not to put out a face-recognition tool out of fear it would be misused. People at Google have indeed confirmed to me that the company has no current plans to release such a system. In fact, Google has gone out of its way to prevent face-recognition in its apps. Google Goggles—the smart-phone app that returns information from the Web when you take a photo of an everyday item—doesn't work on faces. But that's not because it can't work on faces. Google engineers have publicly admitted that, in prototypes, the system is really good at identifying faces. At a conference last year, Google engineer David Petrou said that the system is capable of identifying the face of someone who has as few as 17 other pictures online.* If there are 50 photos, Goggles will be able to get your name almost every time. "We do it well, but it's not deployed," Petrous said.
But Google won't have that luxury forever. Google reps have told me that face-recognition is something that Goggles users have asked for. This isn't surprising—such a tool would be incredibly useful. If you meet someone at a conference, you could point your camera their way and get their contact info. You could snap a group photo at your family reunion and have the pictures automatically filed by name in your photo album. Or you could think of it as Shazam for strangers—who is that woman who's always winking at you on the bus, or that creepy fellow who's leering at you from across the bar? Snap their pictures and find out. Given the demand, and given the widespread availability of the technology, it's inevitable that some company will release such a face-recognition tool very soon. And once the horse leaves the barn, it will become socially acceptable for Google and other tech giants to follow.
What about the privacy fears? What of the possibility that the police will use face-recognition systems to conduct illegal searches, or that con men will use them to find victims, or that, more fundamentally, they'll erase our last shreds of anonymity? These are all legitimate concerns, and indications of how much more annoying (and maybe even terrifying) the world will be to navigate in the face-recognition age. But pointing out the potential abuses of this software—and surely there will be a media outcry—won't make it go away. Technology marches forward and ordinary people—people who will be stalked, thrown in jail, or otherwise harassed on the basis of a facial identified—will be collateral damage.
Soon, though, we'll all learn to live with it. Etiquette and even regulations will develop around when it's OK to point your camera at someone and get her name. It's too late to turn back now: If your face and your name are online today, you've already made yourself searchable. Face-recognition systems simply turn the search on its head—instead of looking for your picture by typing in your name, I can now search for your name by snapping your picture. Don't want yourself searchable, period? You can always get off the Internet, or always leave the house wearing a funny hat and a fake nose.
http://www.slate.com/id/2299134/?from=rss
http://www.slate.com/id/2299134/pagenum/2
Subscribe to:
Comments (Atom)